You might think that cloud services run on never-ending racks of servers and switches in giant datacenters. But what they really run on is trust. Trust that your data (or your client’s data) is absolutely tamper-proof inside that datacenter. Significantly more secure than it would be if you tried to manage the same operations in your own datacenter. Which it absolutely must be. How else could we trust major segments of world economies to the cloud? Software security plays a big role in the cloud but that has to sit on top of highly secure hardware. Compute, storage, networking, everywhere. For this purpose, the Synopsys IP group has solutions tracking the latest security standards and specifications.
Advances in trust standards
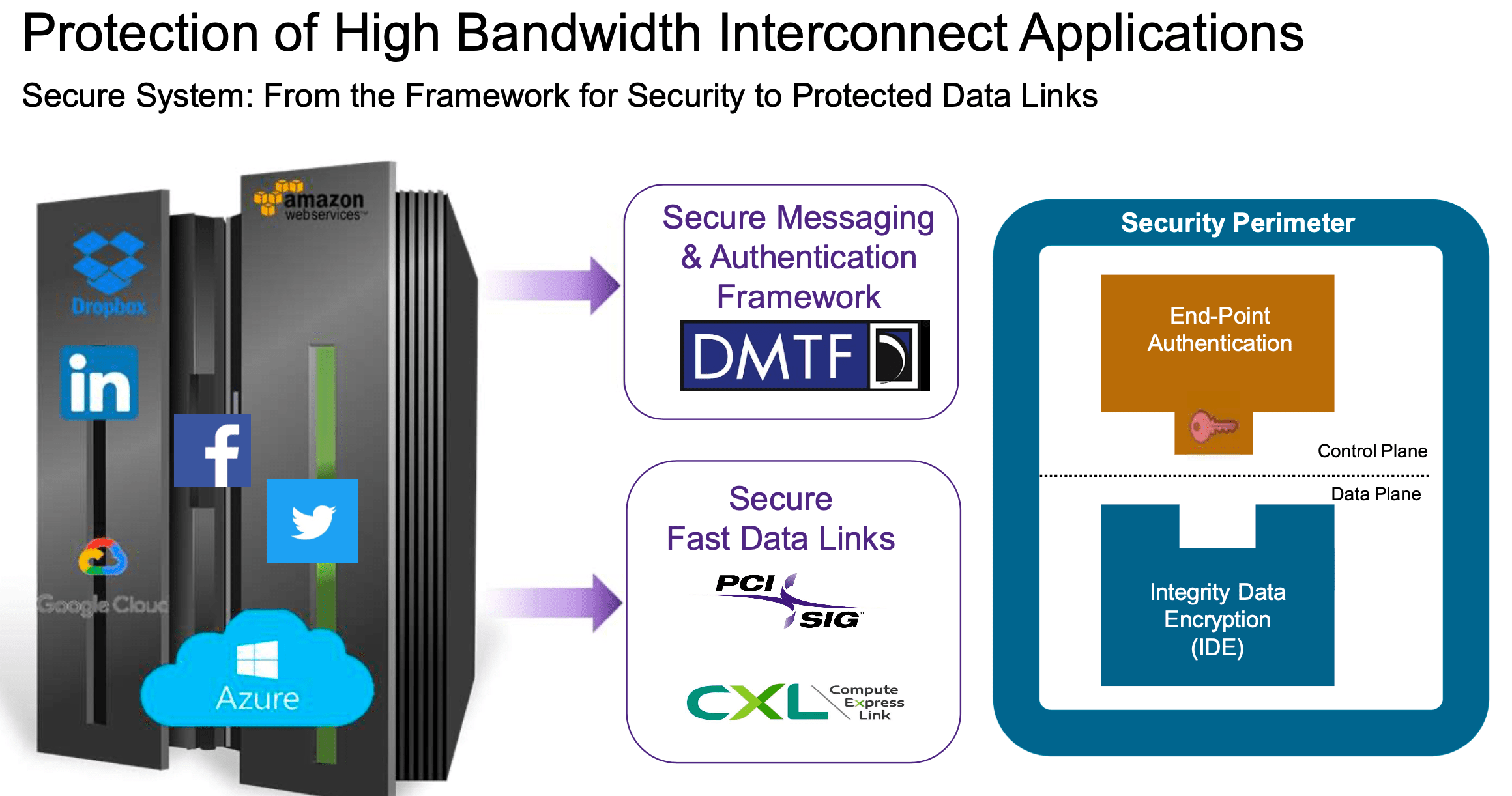
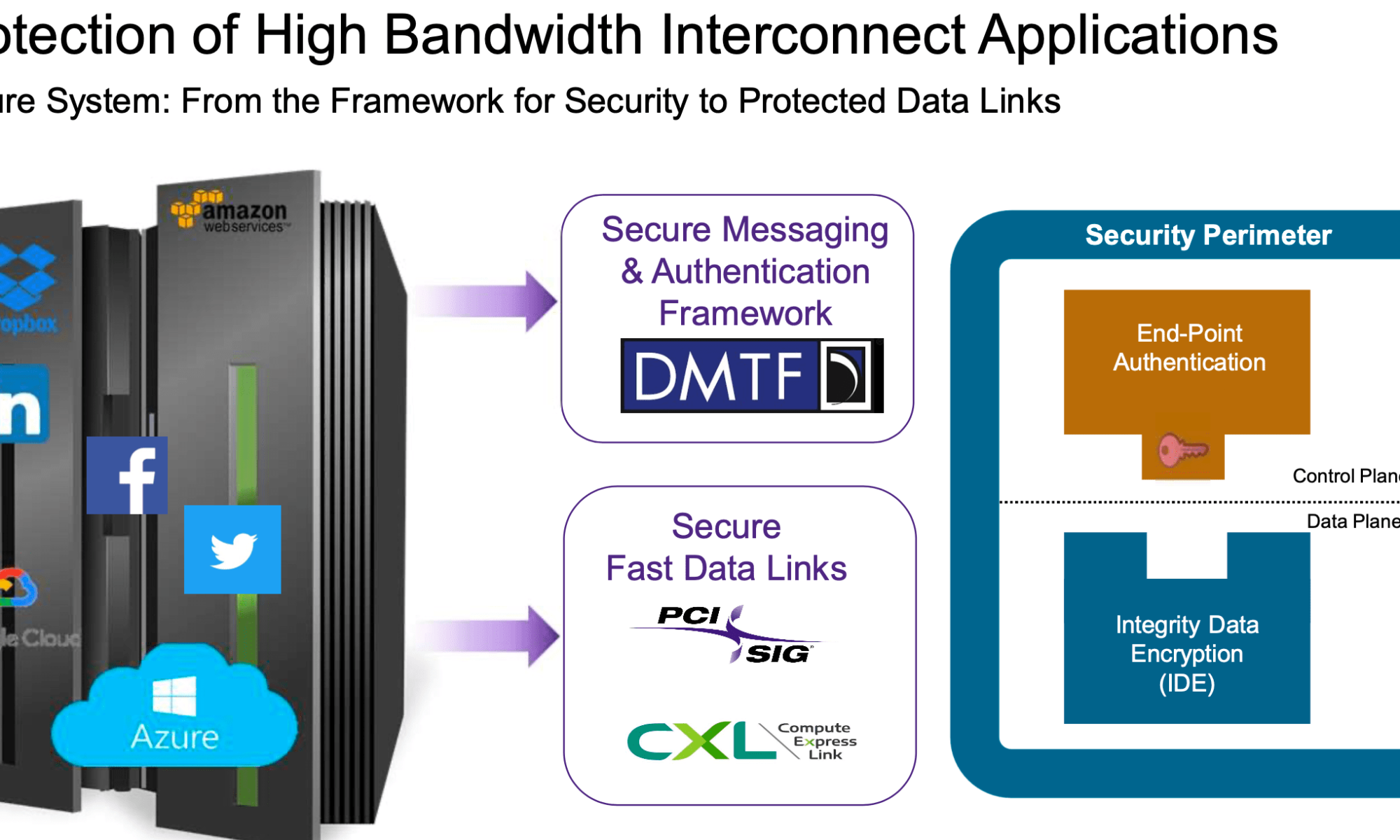
Craig Forward, Security products development lead at Synopsys, recently gave a talk at the Design Reuse and IP virtual conference on this topic. He covered particularly their work on PCIe and CXL security, which includes the end-point messaging and authentication via the Secure Protocol and Data Model (SPDM) developed by the Distributed Management Task Force, and data integrity and encryption via the PCIe and CXL IDE (Integrity and Data Encryption) specifications.
Why this is now so important
That’s an important consideration now that cloud hardware is becoming considerably more heterogenous, no longer simply servers and switches. In a typical cloud network there will be many chips on many linecards which must preserve security, while not compromising throughput. Data transfers between systems (Ethernet, etc.), within systems (PCIe, CXL, custom) and for storage (DDR, NVMe, other). Then there’s GPUs, AI accelerators, the list goes on.
Each of these requires a Hardware Root of Trust (HRoT) and a True Random Number Generator (TRNG), along with support for asymmetric cryptography (RSA and/or ECC) and symmetric cryptography (for example, high performance AES-GCM). Craig talks about how these capabilities can be used to ensure data integrity and encryption security in communication over a PCIe channel between two trusted environments.
Synopsys IP for securing trust
Synopsys provides several hardware/software IP in support of building such solutions. The first is a family of DesignWare tRoot Fx Hardware Security Modules. This is a programmable HRoT based on ARC SEM secure CPU. It offers secure boot, authentication, update, debug and storage, together with crypto acceleration. All sitting inside a high-strength security perimeter. This comes together with a rich set of software security libraries to support multiple protocol implementations.
They also provide an IP for integrity and data encryption (IDE) which will integrate with a PCIe controller to provide PCIe security compliant to the PCIe IDE spec. Similarly, they provide a CXL IDE IP which will bring CXL controller security up to the corresponding CXL IDE standard. Each is based around an AES-GCM crypto engine compliant with the relevant NIST standards, capable of running data widths up to 2048 bits/cycle.
Checkout the talk. Craig provides more detail than I have here.
Also Read:
Synopsys is Extending CXL Applications with New IP
Synopsys talks about their DesignWare USB4 PHY at TSMC’s OIP
Share this post via:





Comments
There are no comments yet.
You must register or log in to view/post comments.