As the threat of quantum computing to modern cybersecurity becomes increasingly real, the technology industry is accelerating efforts to develop cryptographic systems capable of resisting quantum attacks. One of the most significant developments in this field was presented at Embedded World 2026 in Nuremberg, Germany, … Read More
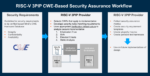
Podcast EP347: Agentic Workflows from Caspia Technologies for Advanced Chip Security Verification with Stuart Audley
Daniel is joined by Stuart Audley, vice president and general manager of product management at Caspia Technologies, where he focuses on agentic security workflows. He has decades of experience designing and deploying cryptographic hardware and security IP for top defense and leading semiconductor companies. He previously… Read More










ASML High-NA EUV is Not Ready for High-Volume Production