Can a combination of learning-based surrogate models plus reachability analysis provide first pass insight into extrema in circuit behavior more quickly than would be practical through Monte-Carlo analysis? Paul Cunningham (GM, Verification at Cadence), Raúl Camposano (Silicon Catalyst, entrepreneur, former Synopsys… Read More
Author: Bernard Murphy
Reachability in Analog and AMS. Innovation in Verification
IP Surgery and the Redundant Logic Problem
It’s now difficult to remember when we didn’t reuse our own IP and didn’t have access to extensive catalogs of commercial IP. But reuse comes with a downside – without modification we can’t finetune IP specs to exactly what we want in a current design. We’re contractually limited in how we can adapt commercial IP, however vendors … Read More
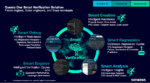
The Siemens Questa plus AI Story Gathers Momentum
I wrote recently about a Siemens pre-announcement at DVCon on their directions in simulation+AI. On May 13th they officially announced a full spectrum of capabilities under the brand Questa One. Abhi Kolpekwar (VP/GM at Siemens EDA) more fully fleshed out the story for me. I asked why Siemens is late to this simulation+AI party.… Read More
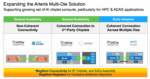
Arteris Expands Their Multi-Die Support
I am tracking the shift to multi-die design, so it’s good to see Arteris extend their NoC expertise, connecting chiplets across an interposer. After all, network connectivity needs don’t stop at the boundaries of chiplets. A multi-die package is at a logical level just a scaled-up SoC for which you still need traffic routing and… Read More
A Novel Approach to Future Proofing AI Hardware
There is a built-in challenge for edge AI intended for long time-in-service markets. Automotive applications are the obvious example, while aerospace and perhaps medical usage may impose similar demands. Support for the advanced AI methods we now expect – transformers, physical and agentic AI – is not feasible without dedicated… Read More
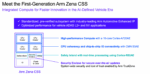
Arm Reveals Zena Automotive Compute Subsystem
Last year Arm announced their support for standards-based virtual prototyping in automotive, along with a portfolio of new AE (automotive enhanced) cores. They also suggested that in 2025 they would be following Arm directions in other LOBs by offering integrated compute subsystems (CSS). Now they have delivered: their Zena… Read More
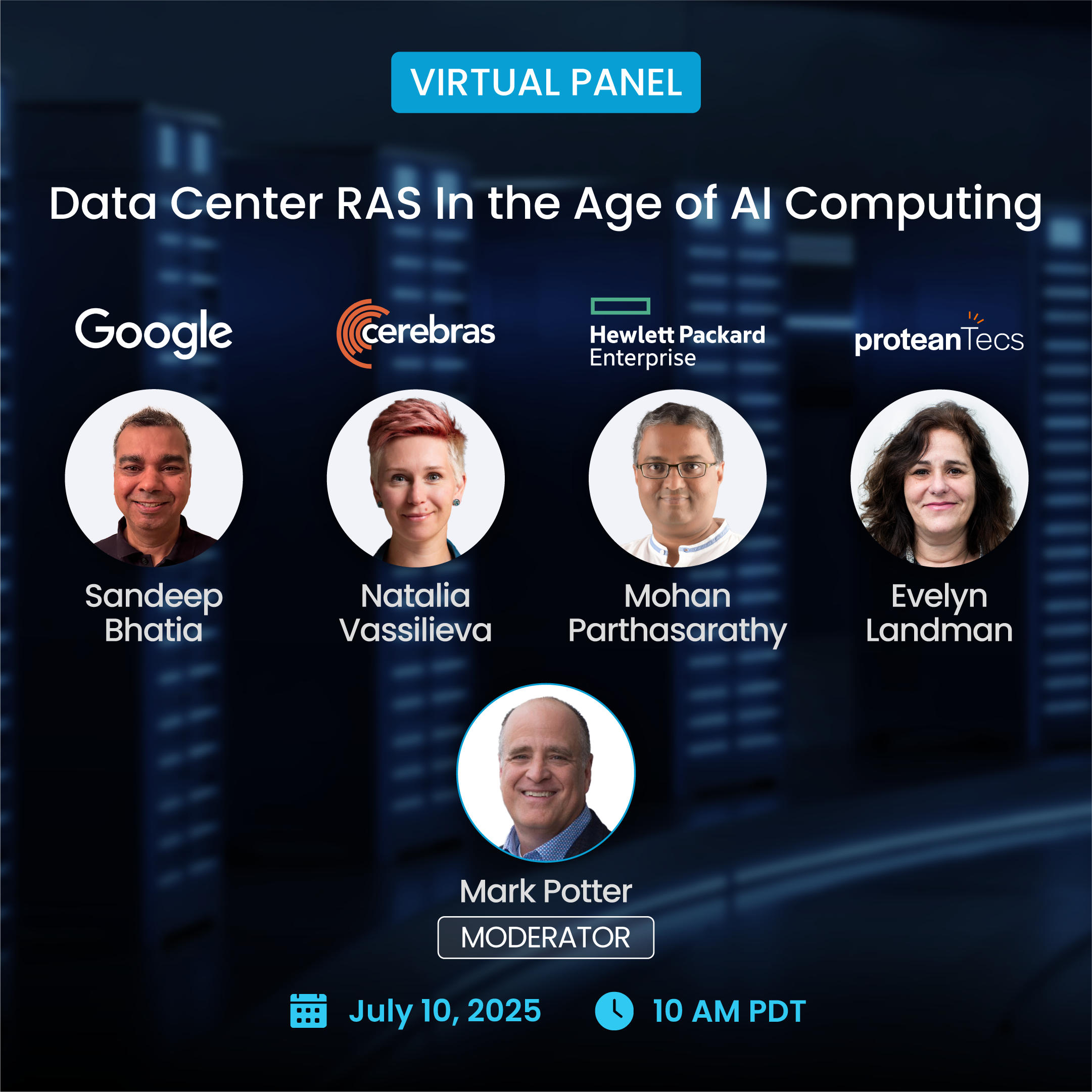
Anirudh Fireside Chats with Jensen and Lip-Bu at CadenceLIVE 2025
Anirudh (Cadence President and CEO) had two fireside chats during CadenceLIVE 2025, the first with Jensen Huang (Founder and CEO of NVIDIA) to kick off the show, and later in the day with Lip-Bu Tan (CEO of Intel). Of course Jensen and Lip-Bu also turn up for other big vendor shows but I was reminded that there is something special about… Read More
Anirudh Keynote at CadenceLIVE 2025 Reveals Millennium M2000
Another content-rich kickoff covering a lot of bases under three main themes: the new Millennium AI supercomputer release, a moonshot towards full autonomy in chip design exploiting agentic AI, and a growing emphasis on digital twins. Cadence President and CEO Anirudh Devgan touched on what is new today, and also market directions… Read More
Optimizing an IR for Hardware Design. Innovation in Verification
Intermediate representations (IRs) between high level languages (C++, AI, etc.) and machine language are both commonplace (witness LLVM) and a continuing active area of research. Paul Cunningham (GM, Verification at Cadence), Raúl Camposano (Silicon Catalyst, entrepreneur, former Synopsys CTO and lecturer at Stanford,… Read More
Turnkey Multi-Protocol Wireless for Everyone
There is no IoT without wireless. If you have a great idea for a world-beating IoT device, you must integrate a wireless module (Bluetooth, Zigbee, Wi-Fi, UWB…) into that device. A ready-made companion wireless chip connected to MCU is one approach but will significantly increase unit cost and reduce profits. Products … Read More











Flynn Was Right: How a 2003 Warning Foretold Today’s Architectural Pivot