I assume you know the Geoffrey Moore “crossing the chasm” concept, jumping from early stage enthusiasts trying your product because they’ll try anything new, to expanding to a mainstream and intrinsically more critical audience – a much tougher proposition. I’d argue there may be more than one of these transitions in the life of a new venture, the first of which can be adoption by a mainstream partner as a part of one of their solutions.
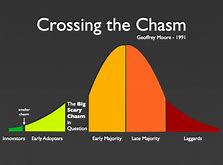
Tortuga, a company that specializes in hardware threat detection and prevention in hardware plus software systems, already had important academic credibility, being birthed from hardware security groups in UCSD and UCSB. They have clients in the semiconductor, aerospace and defense industries, they’re on their second SBIR (small business innovation research) grant, they’ve raised seed funding and last year they received a contract from DARPA to develop new security solutions. All good stuff but feeling like it’s still mostly on the left side of the chasm. Where was mainstream semiconductor support going to come from?
In answer to that question, Tortuga announced just a few weeks ago a partnership with Synopsys. This offers a security verification solution for SoC designs built around the Synopsys DesignWare ARC processor IP and Tortuga’s Radix-S security verification software. Does that mean Synopsys needed extra help to ensure the security of their ARC solutions? Not at all. The unavoidable problem in developing security solutions around any IP is that they depend on the SoC developer not making mistakes in integration. One such example could be a mapping error for the the boundary between secure and insecure operation. Another could be allowing access to secure registers when a debug port has not been correctly disabled. Checking you didn’t make mistakes can become pretty complex, not always easily reducible to assertion VIPs. This is particularly challenging since misbehavior in these cases may be revealed only in interaction between hardware and software over many cycles.
The Tortuga approach to analyzing these integration problems is quite interesting, evolving (as I understand it) from a method called gate-level information flow tracking, coupled with a threat-model in the form of assertions against this analysis. This compiles into verification logic which runs together with your DUT and whatever verification workloads you normally run to check for potential threats as defined by these assertions. I’m told that as long as your verification regressions deliver good general coverage (they’d better at some point), you will have good confidence that these security threats will also have been covered.
Jonny Valamehr (COO at Tortuga) tells me that they and Synopsys have worked together to define a comprehensive set of threat assertions to cover many integration needs. Since an ARC core provides some level of configurability, Jonny said some aspects of the threat model may also need to be configured by the integrator to cover these cases. But I got the impression this isn’t very hard. From what I have seen, threat assertions don’t look so different from SVA assertions, though they express information about paths for assets to flow through the design, rather than logic behaviors. If you’re responsible for security, learning this assertion language doesn’t look like a big barrier.
Jonny tells me that today you buy your ARC core from Synopsys and you buy the Radix-S software from Tortuga. Synopsys and Tortuga have done the development to ensure the technical part of this flow works seamlessly. Making the business flow seamless is still in discussion. Nevertheless, good job Tortuga on taking this important step. You can learn more about Radix-S HERE.
Share this post via:




Comments
There are no comments yet.
You must register or log in to view/post comments.