You are currently viewing SemiWiki as a guest which gives you limited access to the site. To view blog comments and experience other SemiWiki features you must be a registered member. Registration is fast, simple, and absolutely free so please,
join our community today!
WP_Term Object
(
[term_id] => 97
[name] => Security
[slug] => security
[term_group] => 0
[term_taxonomy_id] => 97
[taxonomy] => category
[description] =>
[parent] => 0
[count] => 327
[filter] => raw
[cat_ID] => 97
[category_count] => 327
[category_description] =>
[cat_name] => Security
[category_nicename] => security
[category_parent] => 0
[is_post] =>
)
It was 1976 when distinguished scholars Whitfield Diffie and Martin Hellman published the first practical method of establishing a shared secret-key over an authenticated communications channel without using a prior shared secret. The Diffie-Hellman methodology became known as Public Key Infrastructure or PKI.
That was… Read More
I first met Jason Oberg, CEO and one of the co-founders of Tortuga Logic, several years ago when I was still at Atrenta. At that time Jason and Jonny Valamehr (also a co-founder and the COO) were looking for partners. The timing wasn’t right, but we’ve stayed in touch, for my part because their area of focus (security) is hot and likely… Read More
Disruptive technology and disruptive business models are the lifeblood of the semiconductor industry. My first disruptive experience was with Artisan Components in 1998. The semiconductor industry started cutting IP groups which resulted in a bubble of start-up IP companies including Artisan, Virage Logic, Aspec Technologies,… Read More
Wally Rhines (President and CEO of Mentor, A Siemens Business) has been pushing a contrarian view versus the conventional wisdom that the semiconductor business, and by extension EDA, is slowing down. He pitched this at DVCon and more recently at U2U where I got to hear the pitch and talk to him afterwards.
What causes maturing is… Read More
Asymmetric attacks, like those in cybersecurity, benefit the aggressor by maintaining the ‘combat initiative’. That is, they determine who is targeted, how, when, and where attacks occur. Defenders are largely relegated to preparing and responding to the attacker’s tempo and actions. This is a huge advantage.… Read More
Normally press release events with ARM tend to be somewhat arms-length – a canned pitch followed by limited time for Q&A. Through a still unexplained calendar glitch I missed a scheduled call for a recent announcement. To make up I had the pleasure of a 1-on-1 with Hima Mukkamala, GM of IoT cloud services at ARM. Hima is a heavy … Read More
Technology is reaching a point where it can nearly create fake video and audio content in real-time from handheld devices like smartphones.
In the near future, you will be able to Facetime someone and have a real-time conversation with more than just bunny ears or some other cartoon overlay. Imagine appearing as a person of your … Read More
It has taken the U.S. 16 years to enact Data Breach laws in each state. California led the way, with the first, in 2002 to protect its citizens. Last in line was Alabama, which just signed their law in March 2018. There is no overarching consistent data breach law at the federal level. It is all handled independently by each state. This… Read More
On Thursday April 5th the Design and Reuse SoC IP days continues in Santa Clara at the Hyatt Regency (my favorite hangout). SemiWiki is a co-sponsor and I am Chairman of the IP Security Track. More than 400 people have registered thus far and I expect a big turnout, if you look at the program you will see why. You should also know that registration… Read More
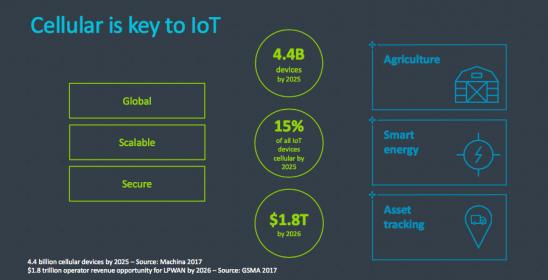
It seems that a hot ticket at Mobile World Congress this year was embedded SIM announcements. As a reminder of why this space is hot, cellular communication for provisioning and data uploads is a very real option for many IoT devices. In agricultural, smart energy and asset tracking applications for example, near-range options… Read More










Captain America: Can Elon Musk Save America’s Chip Manufacturing Industry?