You are currently viewing SemiWiki as a guest which gives you limited access to the site. To view blog comments and experience other SemiWiki features you must be a registered member. Registration is fast, simple, and absolutely free so please,
join our community today!
WP_Term Object
(
[term_id] => 97
[name] => Security
[slug] => security
[term_group] => 0
[term_taxonomy_id] => 97
[taxonomy] => category
[description] =>
[parent] => 0
[count] => 340
[filter] => raw
[cat_ID] => 97
[category_count] => 340
[category_description] =>
[cat_name] => Security
[category_nicename] => security
[category_parent] => 0
[is_post] =>
)
Technology is reaching a point where it can nearly create fake video and audio content in real-time from handheld devices like smartphones.
In the near future, you will be able to Facetime someone and have a real-time conversation with more than just bunny ears or some other cartoon overlay. Imagine appearing as a person of your … Read More
It has taken the U.S. 16 years to enact Data Breach laws in each state. California led the way, with the first, in 2002 to protect its citizens. Last in line was Alabama, which just signed their law in March 2018. There is no overarching consistent data breach law at the federal level. It is all handled independently by each state. This… Read More
On Thursday April 5th the Design and Reuse SoC IP days continues in Santa Clara at the Hyatt Regency (my favorite hangout). SemiWiki is a co-sponsor and I am Chairman of the IP Security Track. More than 400 people have registered thus far and I expect a big turnout, if you look at the program you will see why. You should also know that registration… Read More
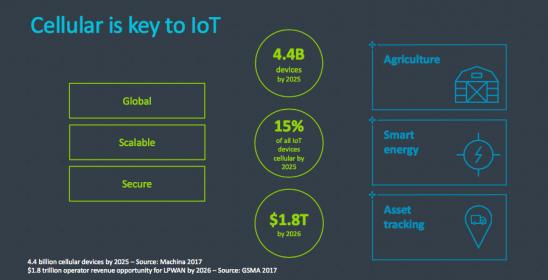
It seems that a hot ticket at Mobile World Congress this year was embedded SIM announcements. As a reminder of why this space is hot, cellular communication for provisioning and data uploads is a very real option for many IoT devices. In agricultural, smart energy and asset tracking applications for example, near-range options… Read More
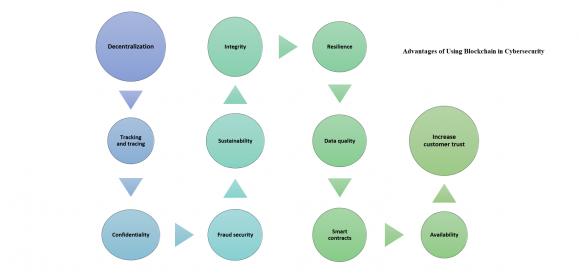
In the first part we covered AI as the first line of defense for cybersecurity, the goal was to keep the cyber-criminals at bay, but in case they managed to get-in and infiltrate the network we need to initiate the second line of defense; #Blockchain. With the fact that cybercrime and cyber security attacks hardly seem to be out of the… Read More
The year 2017 wasn’t a great year for cyber-security; we saw a large number of high-profile cyber attacks; including Uber, Deloitte, Equifax and the now infamous WannaCry ransomware attack, and 2018 started with a bang too with the hackingof Winter Olympics. The frightening truth about increasingly cyber-attacks is … Read More
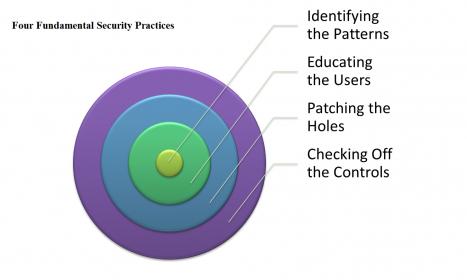
We have become accustomed to the idea that safety expectations can’t be narrowed down to one thing you do in design. They pervade all aspects of design from overall process through analysis, redundancies in design, fault analytics and mitigation for faults and on-board monitors for reliability among other requirements and techniques.… Read More
If you have a phone, you probably know it has a SIM card, for most of us the anchor that ties us into a 2/3-year plan with one network provider, unless you have an unlocked phone. Even then, you have to mess around swapping SIM cards if you travel overseas. Wouldn’t it be nice if the SIM was embedded and could be switched though an app or an… Read More
According to the Economist, “The world’s most valuable resource is no longer oil, but data”. Is this the case?Data is the by-product ofmany aspects of recent technology dynamics and is becoming the currency of today’s digital economy. All categories in Gartner’s Top10 Strategic Technology Trends for 2018 (Figure… Read More
Spoiler alert, the answer is none!
Let me take you back to the beginning to explain that answer.
For the sake of this discussion, I will reduce a complex IoT solution to three fundamental blocks:
- IoT node
- IoT Gateway
- IoT Server
The IoT node is a sensor that converts analog, physical world context into digital data. The node has to have… Read More








Intel: Pushing EMIB Forward: Design Methodology Insights with Synopsys Tools