It turns out that consumers are not alone in their love-hate relationship with SIM cards. SIM cards save us from increasingly widespread cellphone cloning. However, if your experience is anything like mine, it seemed that with every new phone, a new SIM card format was needed. Furthermore, people travelling overseas who wanted to avoid roaming charges often find themselves trying to buy SIM cards in foreign countries (and languages) and then juggling these new cards with their original card to make calls, read texts and more recently pay for purchases.
Consumer gripes aside, there are bigger drawbacks with SIM cards as we know them. Manufacturers encounter higher costs due to the additional parts and the reliability issues associated with the slot and removable card. Also, the IoT has changed the needs for subscriber verification. It’s not just for phones anymore. Expect to see cars, watches, appliances, sensor hubs and almost all manner of connected devices needing unique and secure subscriber identification. Already, it should be clear that these things cannot have SIM cards slots that require manually adding or changing cards every time they are put into service or undergo a service provider change.
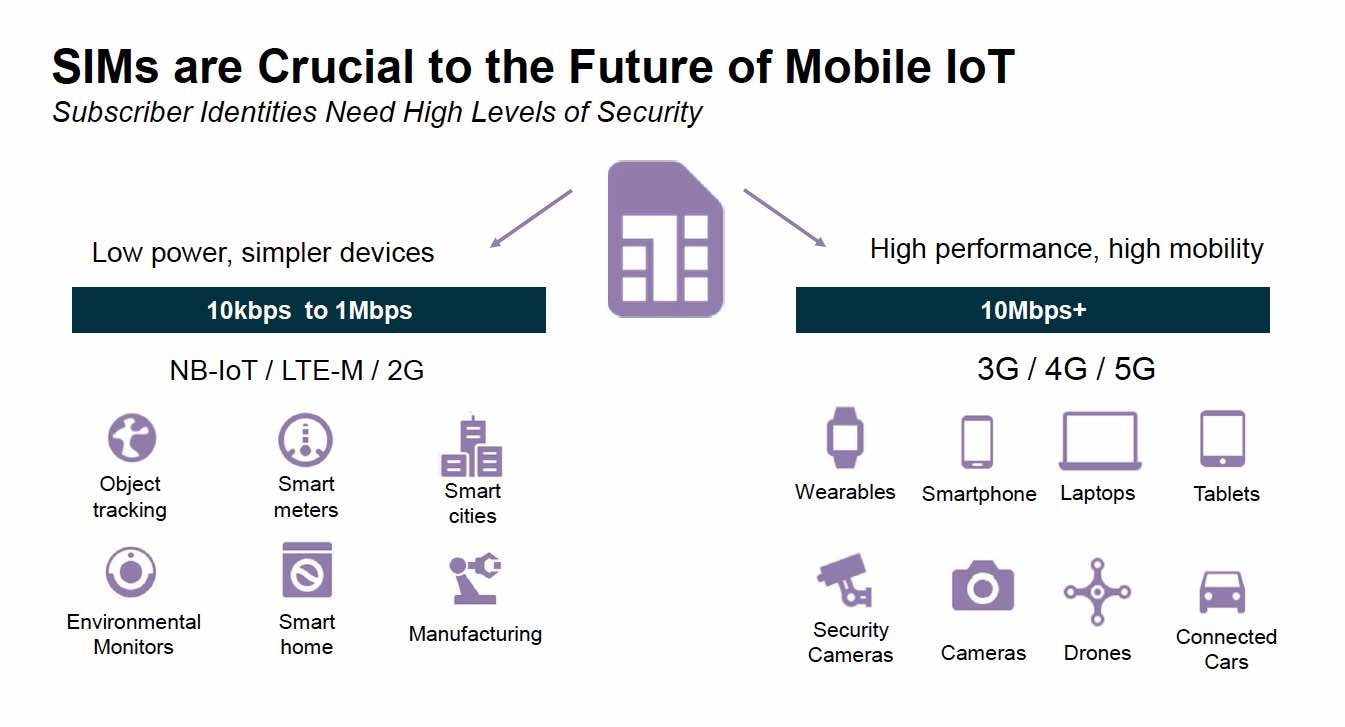 So what is a SIM card anyway? It is really a software application running on a secure processor and a set of security identifiers in the form of a subscriber ID number and an associated encryption key. There is more to it, but for the purposes of this discussion this will suffice. The physical hardware in the card is known as a Universal Integrated Circuit Card (UICC). It contains a CPU, memory and interface hardware. The software that runs on the UICC is called Universal Subscriber Identification Module (USIM) application.
So what is a SIM card anyway? It is really a software application running on a secure processor and a set of security identifiers in the form of a subscriber ID number and an associated encryption key. There is more to it, but for the purposes of this discussion this will suffice. The physical hardware in the card is known as a Universal Integrated Circuit Card (UICC). It contains a CPU, memory and interface hardware. The software that runs on the UICC is called Universal Subscriber Identification Module (USIM) application.
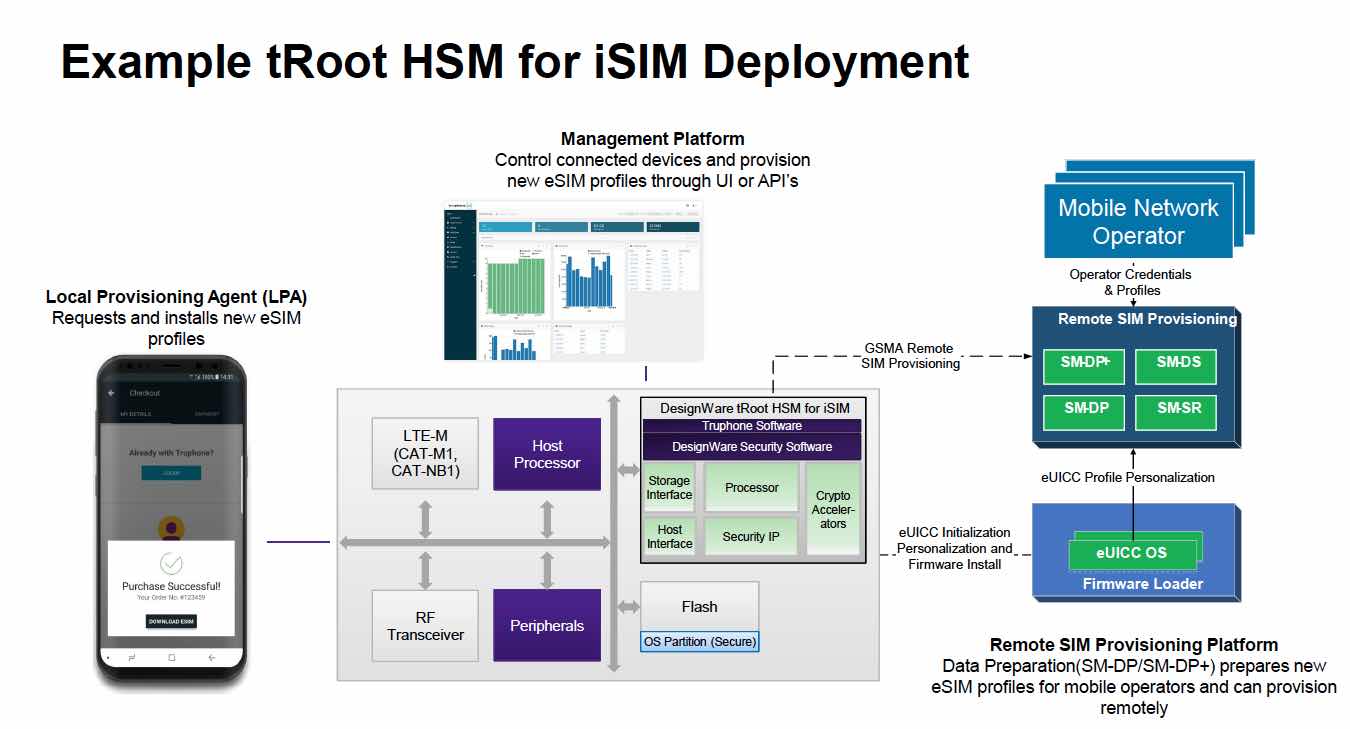
In order to eliminate the need to insert, and subsequently replace, SIM cards, a method is needed to securely bootstrap a permanently built-in UICC and perform a secure Over the Air (OTA) transfer of the subscriber and security information. More than just handset side software and hardware is required to accomplish this. The GSMA has developed a standard for remote SIM provisioning. This has enabled the birth of the eSIM, which uses a UICC that is soldered to the mobile/remote device circuit board. Though, a separate component may still be an issue for some applications because it still takes up valuable board real estate and adds to the BOM.
The next logical step in this evolution is the incorporation of the UICC hardware and software into the system SOC. Synopsys has announced their iSIM, which is a UICC and USIM that can be integrated into any SOC design. Synopsys already has a large portfolio of secure and security related IP, so the addition of this innovative offering will dovetail nicely with their related IP. I recently spoke to Rich Collins, Senior Marketing Manager at Synopsys, about this.
He emphasized that the demands of IoT require moving from a standalone SIM card. IoT designs are already combining the application processor and modem, so including SIM functionality fits the requirements of these IoT systems. To ensure they are offering a complete solution he outlined for me their partnership with Truphone. Rather than leave it to their customers to find and integrate carrier side software to handle the network and OTA provisioning, Synopsys is offering a complete solution that includes the integration with Truphone’s worldwide network. Importantly, end users will have the freedom to choose any local carrier they wish, and Truphone will enable the handoff.
Synopsys is combining many of its mission critical IP components to facilitate iSIM functionality. Among these is their True Random Number Generator (TRNG) which is a vital element to avoid compromised security. Synopsys is integrating Truphone’s eSIM software stack (which includes Javacard OS) in a new tRoot HSM implementation for iSIM.
 With the proliferation of IoT devices, the advent of 5G combined with the many benefits of completely integrated SIM hardware, it is clear that the next year or two will see big changes in SIM implementations. Synopsys is well positioned to help SOC and device designers navigate the process. End users and IoT deployment operators should be pleased with the end results. For more information on the complete Synopsys iSIM offering, visit the product page on their website.
With the proliferation of IoT devices, the advent of 5G combined with the many benefits of completely integrated SIM hardware, it is clear that the next year or two will see big changes in SIM implementations. Synopsys is well positioned to help SOC and device designers navigate the process. End users and IoT deployment operators should be pleased with the end results. For more information on the complete Synopsys iSIM offering, visit the product page on their website.





Comments
There are no comments yet.
You must register or log in to view/post comments.