I’m a believer that connectivity for the IoT at scale (the trillions of devices that the industry predicts) has to be cellular. This is partly based on reach, particularly outside urban areas, but is mostly based on the financial implications of that scale. Yes, you can build infrastructure for say local Wi-Fi support with backhaul to cellular or wired internet, but that comes with capital and on-going operational costs, together with varying levels of quality and security which each organization has to bear. In an age of virtualized everything, this makes no sense. We let the people who specialize in building and running hyperscale datacenters offer us cloud computing. We should let the people who specialize in offering global, interoperable mobile communications (MNOs) provide our IoT communications infrastructure.
This comes with the added benefit that MNOs are motivated to ensure that anyone who connects is authorized to do so, through the authentication services provided by the SIM cards we know so well. SIM cards would be wildly impractical for the IoT – too easy to hack and too painful to maintain across massive networks of edge devices. This has driven development of embedded SIMs (eSIMs), over-the-air (OTA) programmable SIM devices now available in consumer products such as the iPhone XR and XS.
But eSIMs are still separate chips, adding bill of materials cost and power consumption to your product, neither desirable in IoT devices which are generally expected to be very cost-sensitive and depending on very infrequent maintenance to change batteries. The natural next step should be to integrate the eSIM functionality into your SoC, right?
That turned out to be not so easy. I talked to Michael Moorfield, head of Product at Truphone and Ruud Derwig, Sr staff engineer at Synopsys about this. Truphone is an interesting company providing (among other things) an MVNO service (mobile virtual network operator) particularly for international businesses and IoT solution providers needing seamless mobile connectivity around the world. So they know a thing or two about cellular, MNO services and particularly eSIMs. They already provide a full software stack ecosystem for eSIM for the IoT. Now they’ve been working with Synopsys to move this to the next step – integrated SIM (iSIM).
So what’s the big deal in translating an eSIM into an IP? According to Ruud, that’s where this gets tricky. SIMs are held to a very high security standard, much higher than the sadly still common “we should really do something about security in this product” IoT expectation. MNOs don’t want anyone stealing access, from them or from a legitimate customer, since that access is billable; stealing access here connects very directly to stealing money. So SIM security design is very similar to the security you find in chipped credit cards. It needs to be shown to be as near unhackable as we know how to build today (there is no industry standard yet for this, but it wouldn’t be surprising to see one emerge). This means unhackable not just against logical/software attacks, but also against semi-invasive attacks (timing, DPA and RF side-channels) as well as more invasive attacks through power or clock glitching.
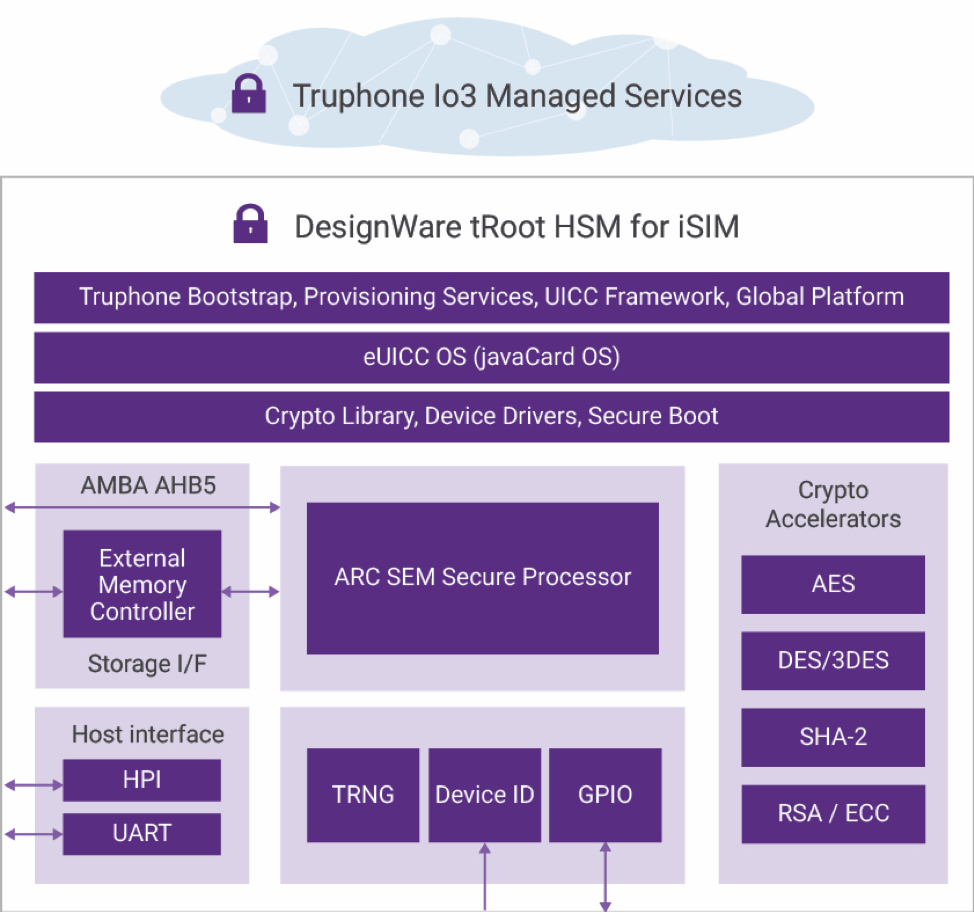
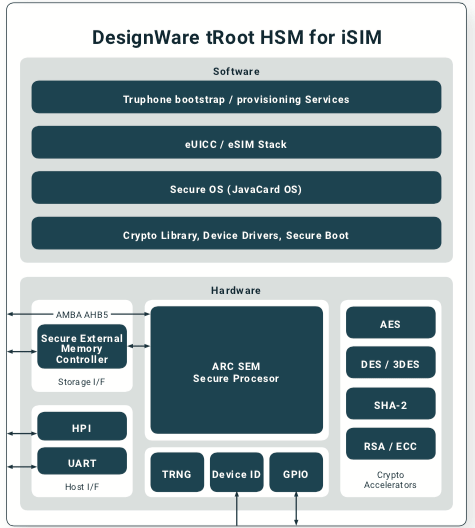
The hardware subsystem has been crafted by Synopsys and Truphone around existing DesignWare components: the ARC SEM processor, crypto accelerators, a secure external memory controller, a true random number generator and other features, all providing multiple mechanisms for protection and tamper detection. Notable in the software stack sitting on top of this hardware is the Java Card platform, the same system used in credit card chips.
Add to this that Truphone is already GSMA-accredited for generating and processing sensitive SIM and MNO data and I have to believe whatever iSIM standards will be, they’ll look pretty much like this solution. You can learn more about this joint development HERE.
Share this post via:






Comments
2 Replies to “Integrated SIMs Will Unlock IoT Growth”
You must register or log in to view/post comments.