Drones attacked an oil processing facility last week and shut down half of all Saudi capacity, representing about 5% of the world’s daily oil production. We have seen how a botnet of compromised home appliances can take down a sizeable chunk of the internet, control structures of electricity and other critical infrastructures… Read More
NATO’s Collective Defense for Cyber Attack Remains Fragile
The Secretary-General of NATO, Jens Stoltenberg, stated all 29 member countries would respond to a serious cyberattack against any of the nations in the coalition. The pressing question is will NATO work together with combined forces when one of the members is attacked in an asymmetrical manner with digital technology?
When… Read More
Cryptocurrencies Should be Enabled to Blacklist Criminal Holdings
Cryptocurrency is seen as a new, wild, reckless, revolutionary, and sometimes shady financial instrument. In addition to legitimate transactions, a disproportionate amount of attention is paid to the criminal use of cryptocurrency to store wealth, collect payments, transfer illicit funds, and launder money. Malicious
Build More and Better Tests Faster
Breker has been in the system test synthesis game for 12 years, starting long before there was a PSS standard. Which means they probably have this figured out better than most, quite simply because they’ve seen it all and done it all. Breker is heavily involved in and aligned with the standard of course but it shouldn’t be surprising… Read More
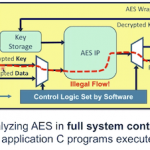
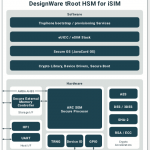
Digging Deeper in Hardware/Software Security
When it comes to security we’re all outraged at the manifest incompetence of whoever was most recently hacked, leaking personal account details for tens of millions of clients and everyone firmly believes that “they” ought to do better. Yet as a society there’s little evidence beyond our clickbait Pavlovian responses that we’re… Read More
Tortuga Webinar: Ensuring System Level Security Through HW/SW Verification
We all know (I hope) that security is important so we’re willing to invest time and money in this area but there are a couple of problems. First there’s no point in making your design secure if it’s not competitive and making it competitive is hard enough, so the great majority of resource and investment is going to go into that objective.… Read More
Banks and ATMs Under Cyber Attack
The Silence hacking crew, mostly attributed to a group of very crafty Russian hackers, has struck again pulling-in over $3 million in cash from ATMs.
At least 3 banks have been attacked in the latest campaign, with Dutch Bangla Bank being the largest. The criminal hackers first compromised the bank’s card management infrastructure… Read More
Integrated SIMs Will Unlock IoT Growth
I’m a believer that connectivity for the IoT at scale (the trillions of devices that the industry predicts) has to be cellular. This is partly based on reach, particularly outside urban areas, but is mostly based on the financial implications of that scale. Yes, you can build infrastructure for say local Wi-Fi support with backhaul… Read More
Google Trustworthy Response to Product Vulnerabilities Demonstrates Leadership
I applaud Google for taking extraordinary steps to protect and service their customers by offering free replacements for the Titan Bluetooth Security Keys. Such product recalls can be expensive, time consuming, and prolong negative stories in the news cycles, yet it is the right thing to do.
Many companies would choose instead
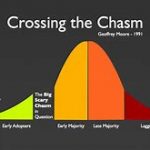
Tortuga Crosses a Chasm
I assume you know the Geoffrey Moore “crossing the chasm” concept, jumping from early stage enthusiasts trying your product because they’ll try anything new, to expanding to a mainstream and intrinsically more critical audience – a much tougher proposition. I’d argue there may be more than one of these transitions in the… Read More








Captain America: Can Elon Musk Save America’s Chip Manufacturing Industry?