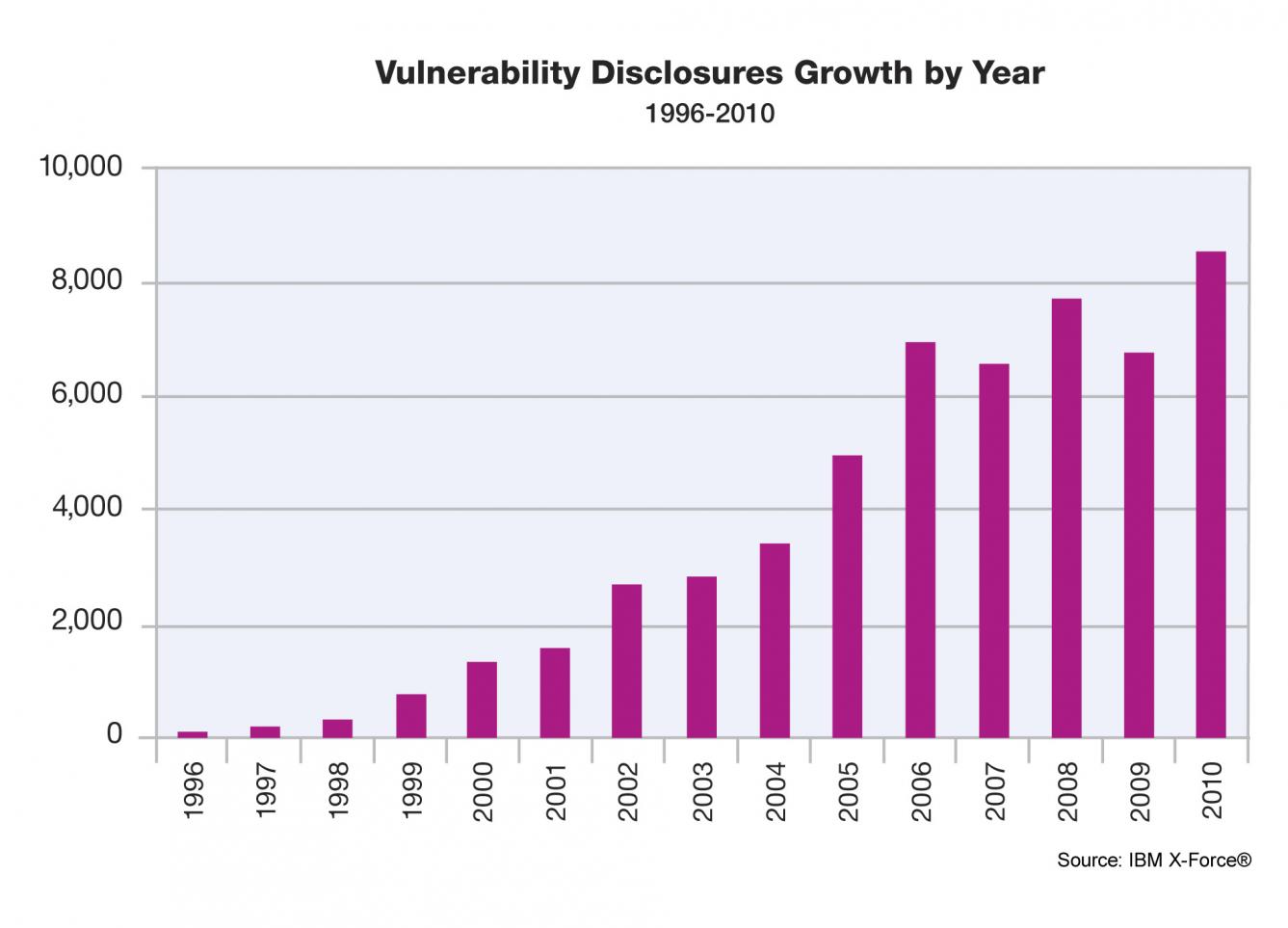
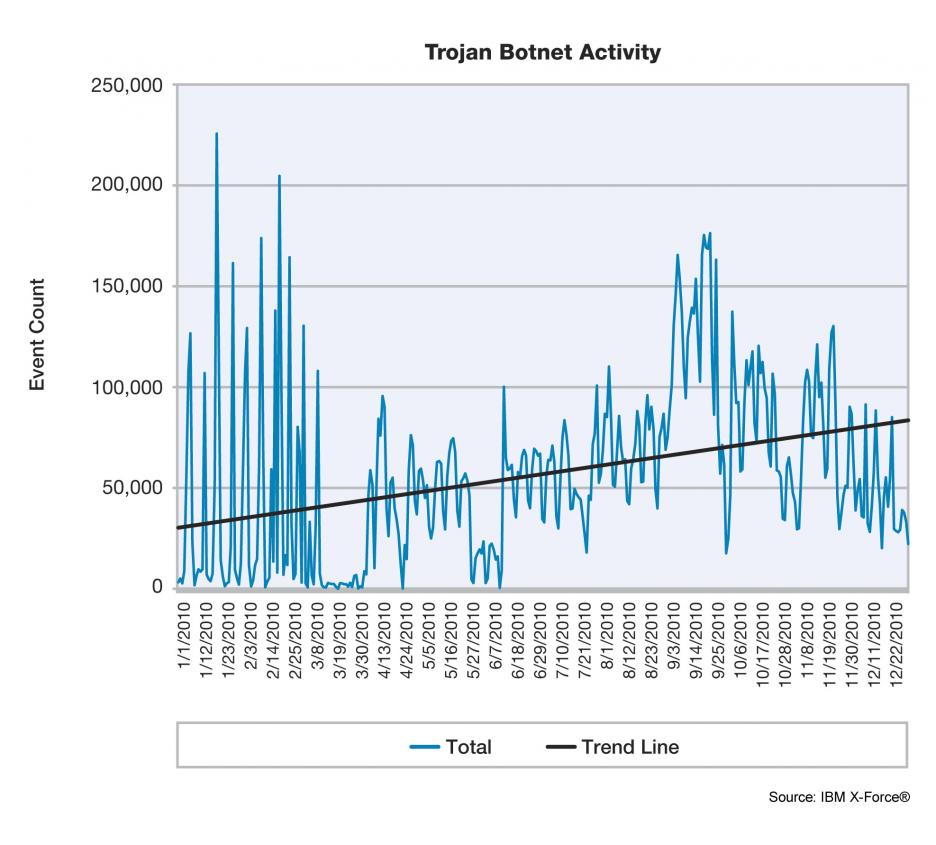
The IBM X-ForceTrend and Risk Report reveals how 2010 was a pivotal year for internet security as networks faced increasingly sophisticated attacks from malicious sources around the world. The X-Force reportedly monitors 13 billion real-time security events every day (150,000 events per second) and has seen an increase in targeted security threats against both government and civilian organizations.
“The numerous, high-profile targeted attacks in 2010 shed light on a crop of highly sophisticated cyber criminals who may be well-funded and operating with knowledge of security vulnerabilities that no one else has,” said Tom Cross, threat intelligence manager at IBM X-Force. “Staying ahead of these growing threats and designing software and services that are secure from the start has never been more critical.”
Last year Iranian nuclear facilities were targeted. It first emerged in September that Iran was battling a powerful computer worm known as Stuxnet, which has the ability to send centrifuges — used in nuclear fuel production — spinning out of control. Different variants of Stuxnet targeted five Iranian organizations, with the probable target widely suspected to be uranium enrichment infrastructure. Iran confirmed that Stuxnet was found on mobile devices belonging to employees.

“Enemies have attacked industrial infrastructure and undermined industrial production through cyber attacks. This was a hostile action against our country,” Gholam Reza Jalali, head of a military unit in charge of combating sabotage, “If it had not been confronted on time, much material damage and human loss could have been inflicted.”
In its 16[SUP]th[/SUP] annual Internet Security Report, antivirus vendor Symantecdetected more than 286 million malware threats last year, signaling a big jump in the volume of automated cyber threats. Symantec gathers data from 240,000 points on the web in more than 200 countries and it gets intelligence from more than 133 million systems that use its antivirus products.
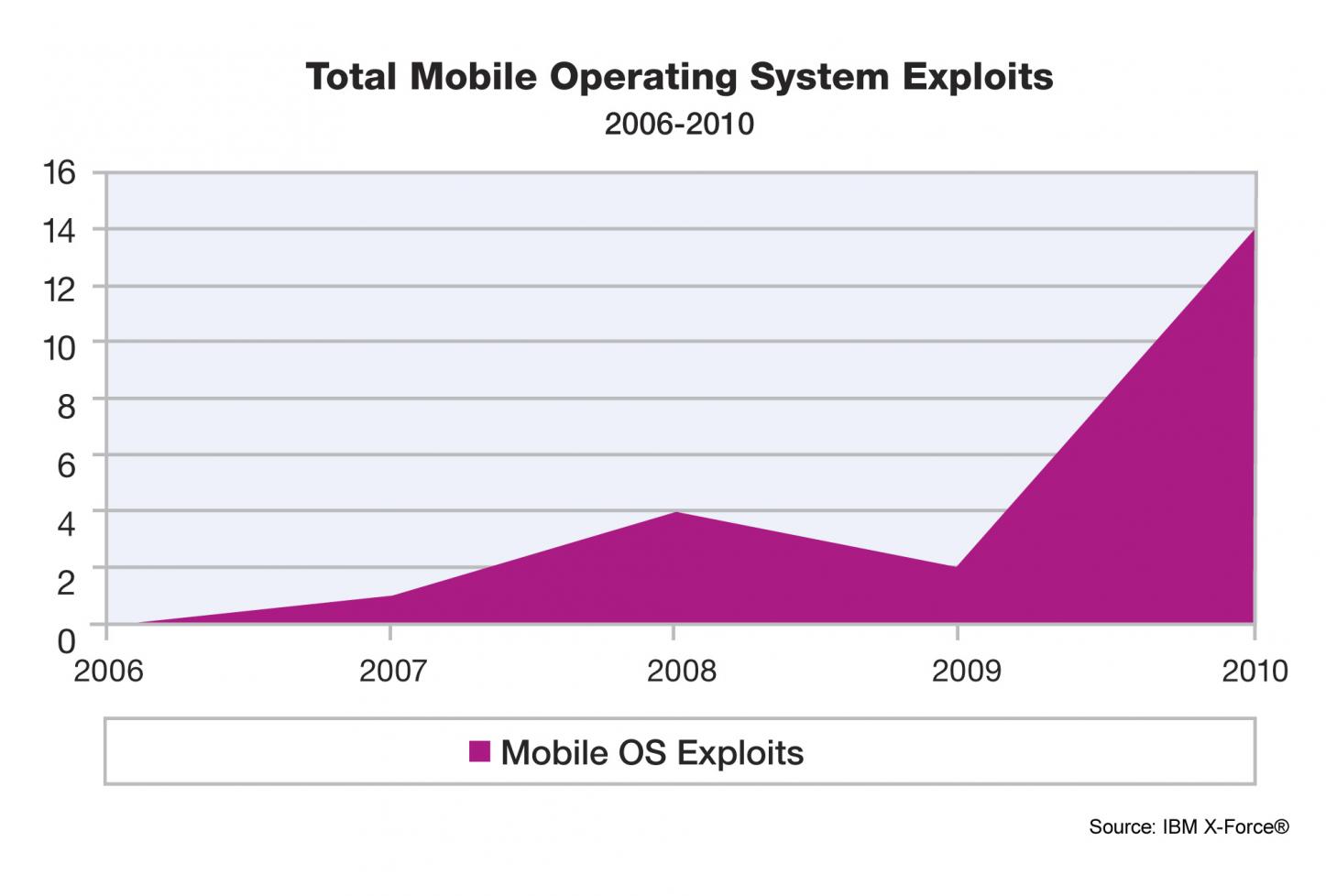
“We’ve seen seismic shifts in things like the mobile landscape,” said Gerry Egan, director of Symantec Research Labs. “The attacks are more sophisticated. There’s still a lot of education that has to happen to reduce the behavior that cybercriminals exploit.”
Last week WordPress.com revealedthat someone gained low-level (root) access to several of its servers and that source code was accessible and “presumed copied”. WordPress.com currently serves 18 million publishers, including VIPs Ebay, TED, CBS, Yahoo! and is responsible for 10% of all websites in the world. WordPress.com itself sees about 300 million unique visits monthly.
“We presume our source code was exposed and copied,” Mullenweg stated on the company’s blog. “While much of our code is open source, there are sensitive bits of our and our partners’ code. Beyond that, however, it appears information disclosed was limited.” Famous last words 😉
So what does this have to do with the semiconductor industry, an industry that is bound by dozens of EDA software vendors, IP companies, and design activity around the world? EVRYTHING! Think about how many people touch, directly and indirectly, an SoC design before tape-out? Use LinkedIn for example: My connections link me to 8,723,184+ people. The security risk probability for the semiconductor design ecosystem is staggering!
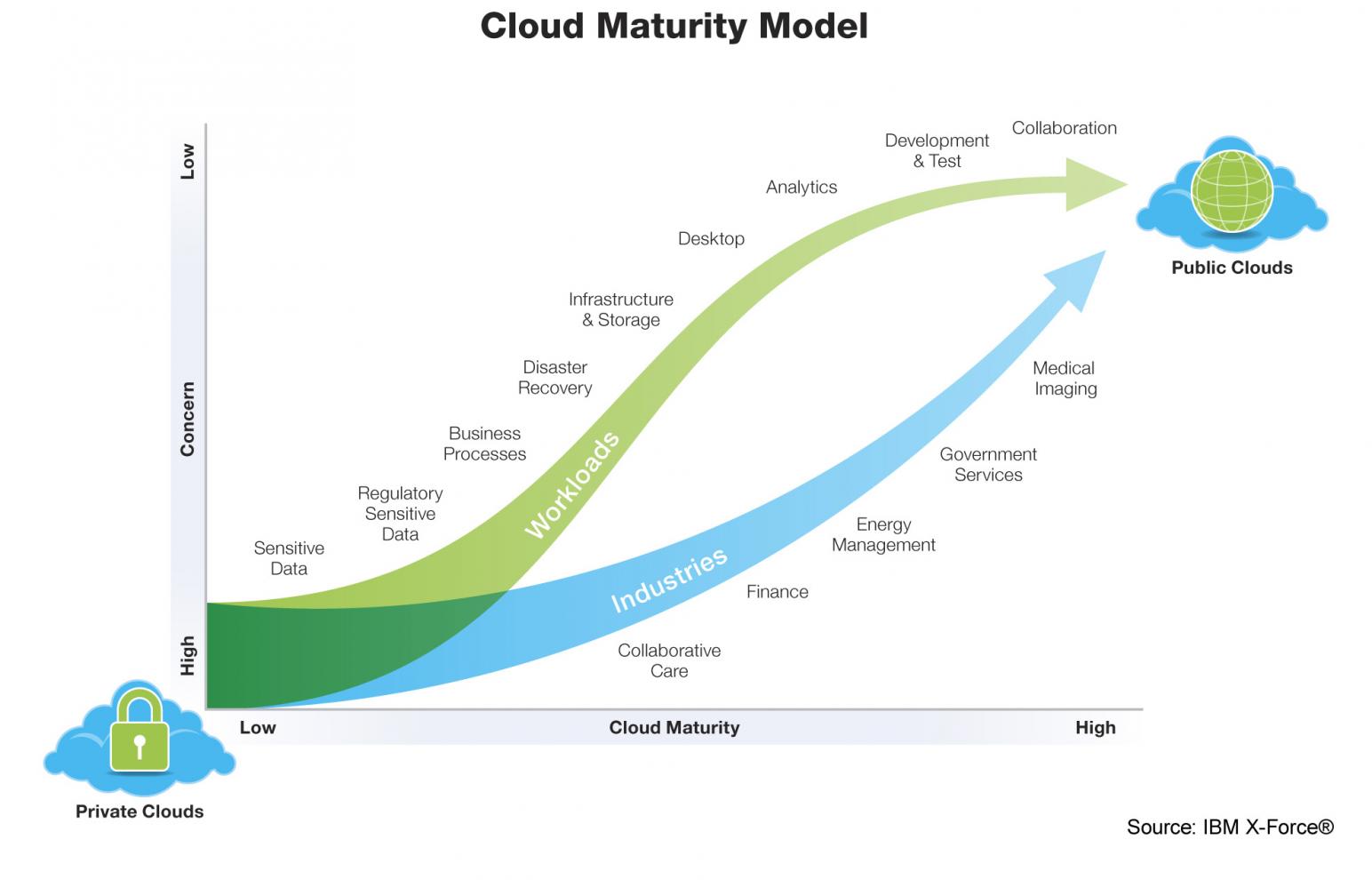
So when I see “security concerns” as the reason why fabless semiconductor companies CHOOSE not to get their designs into the cloud I laugh out loud. My guess is that it will take a catastrophic loss and/or jail time to get the semiconductor executives to protect intellectual property, the true assets of a company. Oh yeah, their financial assets are already safe and sound in the cloud!
Reference: 2011 Semiconductor Forecast: Partly Cloudy!
Share this post via:






Intel: Pushing EMIB Forward: Design Methodology Insights with Synopsys Tools