In today’s increasingly connected world, there are billions of SoCs, powering everything from automotive ECUs to industrial IoT sensors and processing sensitive data. While software-level security is taken seriously, hardware-level vulnerabilities have often been an afterthought. As hackers are now using more complex… Read More
Tag: root of trust
2026 Outlook with Krishna Anne of Agile Analog
Tell us a little bit about yourself and your company.
I have worked in the global semiconductor industry for over 30 years, with major semiconductor companies such as Rambus, AMD and Broadcom, as well as with start-ups such as SCI Semiconductor and DataTrails. I started my career as a digital circuit designer, then moved into marketing,… Read More
Rugged Security Solutions For Evolving Cybersecurity Threats
Secure-IC is a global leader in end-to-end cybersecurity solutions, specializing in the domain of embedded systems and connected devices. With an unwavering commitment to pushing the boundaries of security innovation, Secure-IC has established a remarkable track record. Its credentials include active involvement in new… Read More
Cyber-Physical Security from Chip to Cloud with Post-Quantum Cryptography
In our interconnected world, systems ranging from smart cities and autonomous vehicles to industrial control systems and healthcare devices have become everyday components of our lives. This fusion of physical and digital systems has led to a term called cyber-physical system (CPS). Ubiquitous connectivity is exposing the… Read More
WEBINAR: Flash Memory as a Root of Trust
It should not come as a surprise that the vast majority of IoT devices are insecure. As an indication, one survey estimates that 98% of IoT traffic is unencrypted. It’s not hard to understand why. Many such devices are cost-sensitive, designing security into a product is hard, buyers aren’t prepared to pay a premium for security … Read More
Enlisting Entropy to Generate Secure SoC Root Keys
Most methods of securing SOCs involve storing a root key that provides the basis of all derived keys and encryption of communication. The weakness with these methods is that even if the root key is stored in secure non-volatile memory, there are often methods to read the key. Once a key has been divulged the device can be cloned and … Read More
Securing Applications: A PUFiot Solution for RISC-V-based IoT Devices
In June 2021, eMemory Technology hosted a webinar titled “PUFiot: A PUFrt-based Secure Coprocessor.” You can read a blog leading up to that webinar here. PUFiot is a novel high-security crypto coprocessor. You can access a recording of that entire webinar from eMemory’s Resources page. While the focus of that webinar was to present… Read More
Digging Deeper in Hardware/Software Security
When it comes to security we’re all outraged at the manifest incompetence of whoever was most recently hacked, leaking personal account details for tens of millions of clients and everyone firmly believes that “they” ought to do better. Yet as a society there’s little evidence beyond our clickbait Pavlovian responses that we’re… Read More
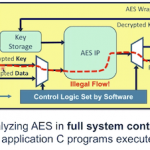
SOC security is not a job for general purpose CPUs
Life is full of convenience-security tradeoffs. Sometimes these are explicit, where you get to make an active choice about how secure or insecure you want things to be. Other times we are unaware of the choices we are making, and how risky they are for the convenience provided. If you leave your bike unlocked, you can expect it to be… Read More
Drop-In Security for IoT Edge Devices
You’re excited about the business potential for your cool new baby monitor, geo-fenced kid’s watch, home security system or whatever breakthrough app you want to build. You want to focus on the capabilities of the system, connecting it to the cloud and your marketing rollout plan. Then someone asks whether your system is architected… Read More