This is the first in a series of CEO interviews and I thought semiconductor IP would be a great place to start. Xerxes Wania is the President and CEO of Sidense, a leading developer of Non-Volatile Memory (NVM) One-Time Programmable (OTP) IP cores. Sidense has been a part of SemiWiki since 2013 so we know them quite well. I hope the rest… Read More
IOT Security – Ongoing Challenge
It is near impossible to read or have a conversation about IoT, without security becoming a major topic. For IT professionals involved with IoT projects, security needs to be a major consideration, starting with planning and design, and continuing all the way through to deployment, implementation, and maintenance. Security… Read More
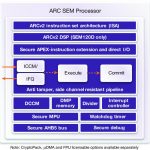
A Powerful Case for the ARC SEM Processor
Building devices for the IoT has become especially challenging thanks to two conflicting requirements. The device has to be small and ultra-low power in most applications but also in many of those applications it has to provide a high-level of security, especially to defend high-value targets like smart metering, payment terminals,… Read More
Using Blockchain to Secure IoT
IoT is creating new opportunities and providing a competitive advantage for businesses in current and new markets. It touches everything—not just the data, but how, when, where and why you collect it. The technologies that have created the Internet of Things aren’t changing the internet only, but rather change the things connected… Read More
We Have Met the Enemy (of Security) and It Is Us
(With apologies to Pogo.) For all the great work that we are seeing in improving both software and hardware security, we – not the technology – are in many ways the weakest link in the security chain. Recent reports indicate we are surprisingly easy to fool, despite our much proclaimed awareness of risks.
In a recent experiment at … Read More
Semi execs look at IoT tradeoffs a bit differently
What happens when you get a panel of four executives together with an industry-leading journalist to discuss tradeoffs in IoT designs? After the obligatory introductions, Ed Sperling took this group into questions on power, performance, and integration.… Read More
Lethal data injection a much bigger threat
Watching a spirited debate on Twitter this morning between Tom Peters and some of his followers reminded me of the plot of many spy movies: silently killing an opponent with a lethal injection of some exotic, undetectable poison. We are building in enormous risks in more and more big data systems.… Read More
Establishing Principles for IoT Security
Much has been said about the potential of IoT. So much so, that it is has been featured at the peak of inflated expectations on Gartner’s hype cycle for quite some time. As the hype inevitably subsides, the reality of delivering the benefits of IoT grows, and the initial excitement turns to concern. Challenges around security and … Read More
Industry Analyst Perspectives On The Apple WWDC 2016 Keynote
I was in-person and live at Apple’s WWDC keynote in San Francisco. The following are my quick takeaways from the event.
Watch and watchOS:
Apple is focusing on exactly what they should be with watchOS, and that’s speed, ease of use and upping the ante in health and fitness. With the first Watch and watchOS, Apple solved many of the problems… Read More
SMART sensors with OTP memory for the IIoT
A few years back before IoT became the buzzword, the industrial automation community had already talking about “smart sensors” since the mid-1990s. The impetus for those discussions was IEEE 1451, a family of standards for adding intelligence and wireless communications to sensors so they could be incorporated into field networks.… Read More



SoC PLANNER: A New Generation of SoC Design Exploration Solution Managing Cost-effectiveness and Sustainability