I get frustrated by shortsighted perceptions, which are misleading and dangerous is far easier to vilify something people don’t fully understand.
Here is another article, titled Bitcoin is Aiding the Ransomware Industry, published by Coindesk, implying cryptocurrency is the cause of digital crime.
This is one of many such… Read More














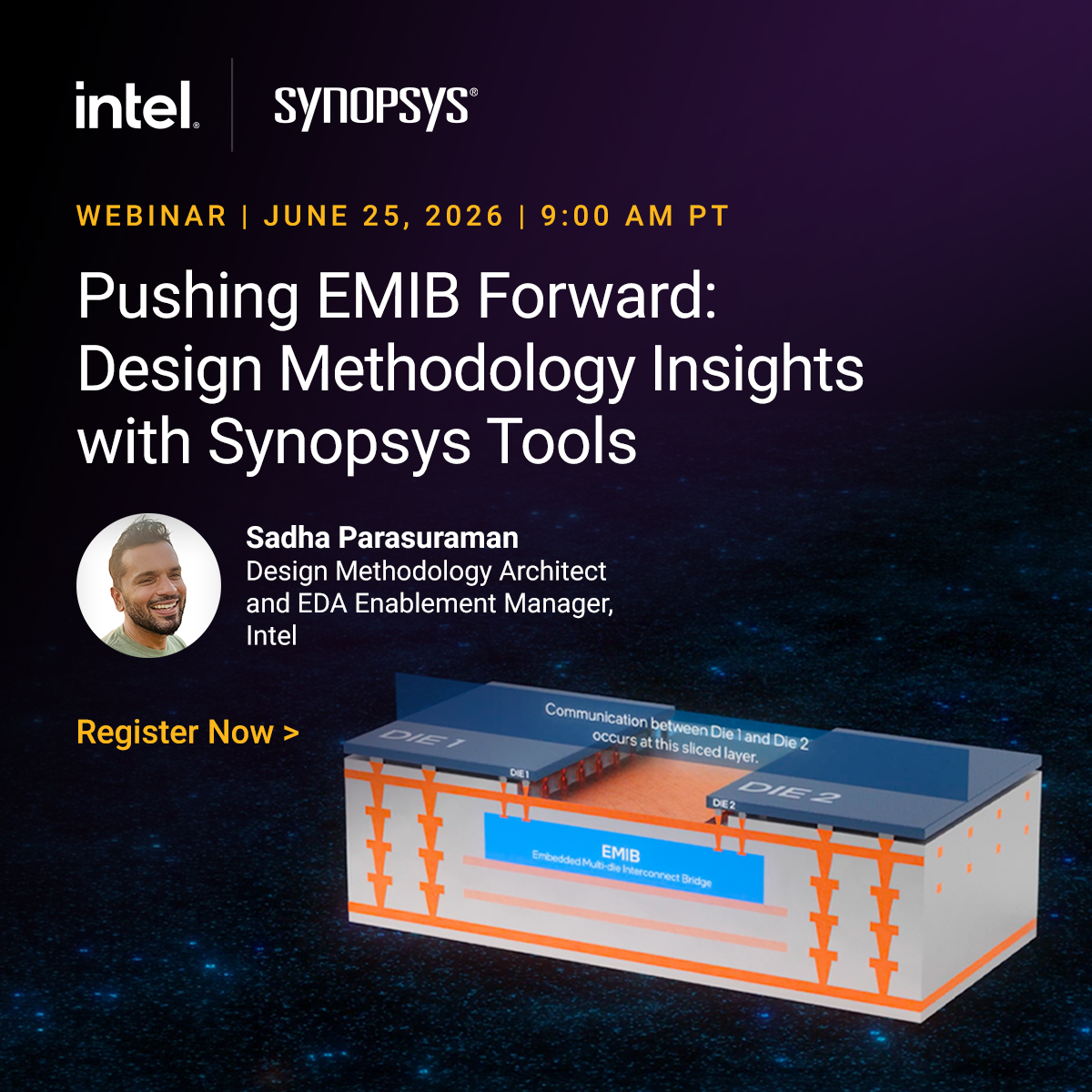





Intel: Pushing EMIB Forward: Design Methodology Insights with Synopsys Tools