Anybody who’s ever read the iconic MAD magazine would be familiar with the wordless Spy vs Spy cartoon. First published in January, 1961, it features two agents involved in stereotypical and comical espionage activities. One is dressed in white, and the other in black, but they are otherwise identical. A parody of the political… Read More
Author: Bill Montgomery
Having Your Digital Cake and Eating It Too
You Can’t Get There From Here
No doubt many who read this article have heard the expression “You can’t get there from here…” It’s most often attributed to New Englanders – primarily residents of Maine – to describe a route to a destination that is so circuitous and complex that one needn’t bother embarking on the journey.
In the context of the business world, the… Read More
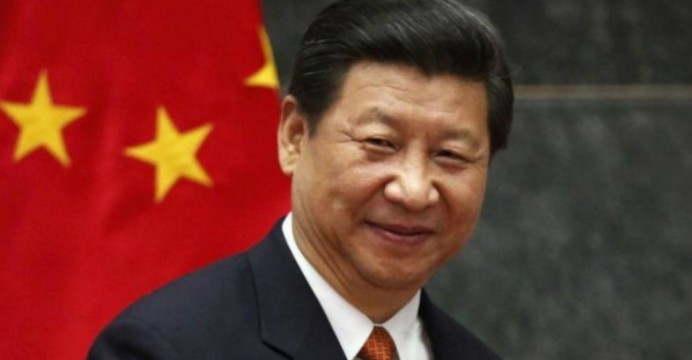
Restoring Digital Trust – Can China Lead the Way?
I read with interest the US Chamber of Commerce’s assessment of the Made in China (MIC) 2025 plan to transform the world’s most populous nation into an Advanced Manufacturing leader. MIC 2025 covers 10 strategic industries that China identifies as critical to economic growth in the 21[SUP]st[/SUP] century, including next-gen… Read More
Is This the Death Knell for PKI? I think so…
It was 1976 when distinguished scholars Whitfield Diffie and Martin Hellman published the first practical method of establishing a shared secret-key over an authenticated communications channel without using a prior shared secret. The Diffie-Hellman methodology became known as Public Key Infrastructure or PKI.
That was… Read More
Lipstick on the Digital Pig
I have a lot of friends in the real estate industry, and two of the most common sales tactics are to create “curb appeal,” and to “stage” the interior of the residence being sold. Curb appeal, of course, refers to making the home looks as appealing as possible upon first impression. Update the landscaping. Add flowers. Make sure the… Read More
Think your future historical encrypted data is secure? Think again…
It’s been 32 years since the successful sci-fi comedy, Back to the Future, saw 17-year old Marty McFly – played by Michael J. Fox – accidentally travel 30 years back in time to 1955. The film was a box-office smash, as audiences worldwide delighted in McFly’s antics, only to soon realize that the cool kid from the future was jeopardizing… Read More
The IoTrojan Horse – an army of toasters
Most everybody is familiar with the term Trojan Horse, drawn from Greek mythology. It’s a tale from the Trojan War where, after a fruitless 10-year attempt to capture the city of Troy, the Greeks constructed a huge wooden horse, left it outside the city walls, and then sailed away, seemingly accepting defeat. The Trojans were elated,… Read More
The CyberSecurity Emperor Has No Clothes
In the past year, I’ve written numerous articles that have a common theme: the security world is badly broken as crypto schemas developed in the 90’s are no defense for today’s sophisticated hackers. For the most part, my blogs have been very well received, and have been picked up and posted by multiple sites and publications worldwide.… Read More
e-Armageddon
CNN: International, Final Report. Wednesday, December 25th, 2019 : The events that have unfolded in the last 72 hours have devastated the entire civilized world, and have left society as we know it on the brink of collapse. I’m told that our networks are now shutting down, and that the report I am about to file will be likely be the final… Read More
Crypto Key Exchange …like taking candy from a digital baby
For those among you who have read my previous SemiWiki articles, you will no doubt see a theme: the security of our connected world is badly broken, and for the bad guys, violating our online lives – both business and personal – is as easy as taking candy from the proverbial baby.… Read More













Captain America: Can Elon Musk Save America’s Chip Manufacturing Industry?