Tell us a little bit about yourself and your company.
I have worked in the global semiconductor industry for over 30 years, with major semiconductor companies such as Rambus, AMD and Broadcom, as well as with start-ups such as SCI Semiconductor and DataTrails. I started my career as a digital circuit designer, then moved into marketing,… Read More
Learn from leading hardware security researchers & professionals and discuss
the latest & most innovative research on attacking and defending hardware.
Connect with industry peers. Join us for a bigger, bolder, and better hardwear.io.
ARE YOU READY FOR HARDWEAR.IO USA 2026?
In the past couple of months our goal was
…
Read More
The premier symposium that facilitates the rapid growth of hardware-based security research and development. Since 2008, HOST has served as the globally recognized event for researchers and practitioners to advance knowledge and technologies related to hardware security and assurance.
May 4 – 7 2026
Washington DC, USA
Hardware-level chip security has become an important topic across the semiconductor ecosystem. Thanks to sophisticated AI-fueled attacks, the hardware root of trust and its firmware are now vulnerable. And unlike software security, an instantiated weakness cannot be patched. The implications of such vulnerabilities are… Read More
Just got an opportunity to write a blog on PQShield, and I’m delighted for several reasons. Happy to work with a company based in Oxford and happy to work on a quantum computing-related topic, which you’ll find I will be getting into more deeply over coming months. (Need a little relief from a constant stream of AI topics.) Also important,… Read More
For decades, chip design has been a delicate balance of creativity and drudgery. Architects craft detailed specifications, engineers read those documents line by line, and teams write and debug thousands of lines of Verilog and UVM code. Verification alone can consume up to 35 percent of a project’s cost and add many months to … Read More
We have a shortage of reference designs to test detection of security vulnerabilities. An LLM-based method demonstrates how to fix that problem with structured prompt engineering. Paul Cunningham (GM, Verification at Cadence), Raúl Camposano (Silicon Catalyst, entrepreneur, former Synopsys CTO and lecturer at Stanford,… Read More
The moral of today’s story is that to succeed in a late-adopter market, sometimes you just have to wait for the market to catch up (assuming you have a strong early adopter market to buy your product today). I have been working with Arteris for 6+ years now promoting their NoC technology, and there was never any question that they offer… Read More
Mixed-signal and analog design are key aspects of modern electronics. Every chip incorporates some form of analog IP, as even digital logic is dependent on analog signals for critical functions. Many digital design engineers are known to be uncomfortable with the prospect of integrating analog components. However, the current… Read More
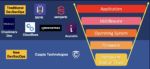
Semiconductor intellectual property (IP) plays a critical role in modern system-on-chip (SoC) designs. That’s not surprising given that modern SoCs are highly complex designs that leverage already proven building blocks such as processors, interfaces, foundational IP, on-chip bus fabrics, security IP, and others. This… Read More