by Jagadish Nayak
RISC-V adoption continues to accelerate across commercial and government microelectronics programs. Whether open-source or commercially licensed, most RISC-V processor cores are integrated as third-party IP (3PIP), potentially introducing supply chain security challenges that demand structured, design-level assurance.
As systems become more heterogeneous and interconnected, design supply chain security is no longer a documentation exercise, but an engineering challenge. A single weakness in processor IP can cascade into systemic risk. That reality makes scalable, repeatable 3PIP assurance essential, especially for RISC-V cores deployed in mission-critical environments.
From Third-Party IP Risk to Repeatable Assurance
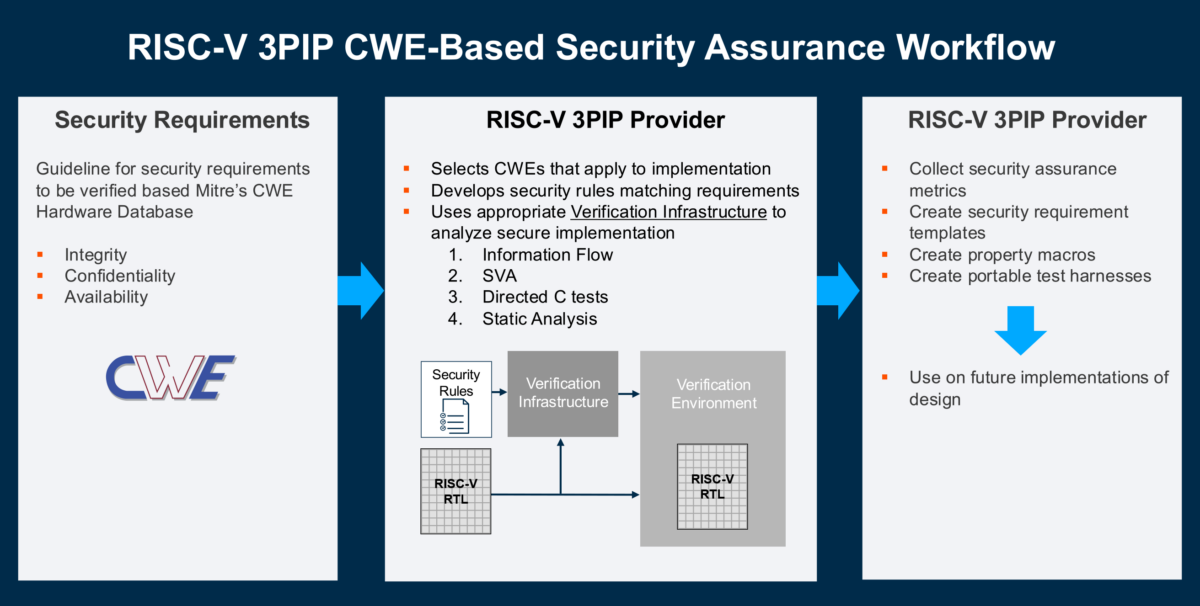
Traditional IP integration workflows often rely on vendor claims, checklist-based reviews, and limited test evidence. While helpful, these approaches rarely provide design-level assurance across all relevant weakness classes. To address this gap, a Common Weakness Enumeration (CWE)-based methodology enables structured, measurable, and portable security validation.
A structured CWE-based methodology replaces ad hoc reviews with measurable validation. Relevant weaknesses are scoped from the MITRE database, translated into security requirements, verified through executable properties and tests, and captured as traceable assurance artifacts.
The outcome is not simply test coverage, but documented security assurance tied directly to recognized weakness definitions.
Scaling Assurance for the RISC-V Ecosystem
RISC-V’s consistent ISA foundation enables reusable security requirement templates, parameterized verification properties, and portable C-based test workloads. Once developed, these artifacts can be applied across multiple RISC-V cores with minimal modification, significantly reducing non-recurring engineering (NRE) effort.
The benefits of templatizing CWE-derived security requirements for RISC-V processors include:
- Teams can avoid starting from scratch for each integration.
- Scope inclusion decisions can be repurposed.
- Verification properties can be parameterized for specific RTL implementations.
- C-based tests can be compiled using standard RISC-V toolchains and reused across multiple cores with minimal modification.
This portability is particularly powerful for programs integrating multiple RISC-V implementations across product lines or lifecycle revisions.
Demonstrated Use Case: SiFive X280 3PIP Assurance
In a collaboration between Cycuity (an Arteris brand), SiFive, and BAE Systems, the methodology was applied to a commercial RISC-V core integrated into a larger SoC. Of 60 CWEs identified as potentially in scope, 16 have been analyzed using templated security requirements and reusable verification infrastructure spanning information-flow rules, static analysis, portable C-tests, and assertion-based verification.
What the Results Reveal
Of the 16 CWEs analyzed:
- 12 were confirmed passing under the defined requirements.
- 3 were flagged as failing by rule definition.
- 1 was determined to be out of scope after deeper analysis.
Importantly, failing a CWE does not inherently indicate a vulnerability—it highlights divergence from formal CWE definitions and prompts system-level evaluation of mitigation strategy.
For example, evaluation of debug-mode transitions revealed that sensitive registers are not automatically cleared when entering debug mode. While architecturally intentional, this behavior required software mitigation planning at the system level. Similarly, analysis of register reset conditions identified registers not explicitly initialized at reset. Although deemed non-critical in context, the structured analysis ensured no assumptions were left unvalidated.
These findings highlight an essential point: assurance is not simply about finding flaws, but it is about eliminating uncertainty. Engineers and managers alike gain clearer visibility into implementation behavior, design intent, and mitigation boundaries.
Reducing NRE Through Reusable Assurance Templates
One of the most valuable outcomes of the RISC-V initiative is measurable reduction in assurance effort. Once security requirement templates, property macros, and portable test harnesses are defined, subsequent RISC-V cores can be evaluated with significantly reduced engineering investment. The methodology enables acceleration without sacrificing rigor.
Verification teams can focus effort where differentiation truly exists, such as implementation-specific signals, privilege modes, memory maps, and integration boundaries, rather than recreating foundational security requirements. For government and defense programs under Trusted and Assured Microelectronics (T&AM) objectives, this repeatability directly supports both technical assurance and program schedule constraints.
Strengthening the Design Supply Chain for RISC-V
As microelectronics ecosystems diversify, design supply chains now span open-source repositories, commercial IP vendors, integrators, tool providers, and system-level developers. Supply chain security cannot be enforced solely at procurement but must be embedded within the design verification lifecycle.
CWE-based assurance provides a shared technical language across stakeholders, for instance:
- IP providers can align their documentation and artifacts to standardized weakness definitions.
- Integrators can demand traceable evidence.
- System architects can quantify residual risk and implement deliberate mitigations.
This transparency strengthens collaboration without exposing proprietary RTL or design details unnecessarily.
Looking Ahead: Expanding Beyond RISC-V
While this work focuses on RISC-V, the methodology generalizes to any third-party IP, from processors to accelerators and peripherals. Assurance will never be zero cost, but structured, reusable frameworks transform it from reactive compliance into a scalable engineering discipline. For organizations building on RISC-V and beyond, this shift is foundational to safeguarding modern design supply chains.
As RISC-V deployment continues to grow in high-assurance and mission-critical systems, design teams must move beyond trust-by-assumption. Comprehensive, CWE-based 3PIP verification enables measurable confidence, reduces integration uncertainty, and strengthens the entire microelectronics ecosystem from IP provider to end system.
CONTACT ARTERIS
Jagadish Nayak is a Distinguished Engineer in Security at Arteris (formerly Cycuity). He provides technical expertise and guidance on the Hardware Security Verification and the Radix family of tools for security verification. He has an extensive background in hardware design, verification and security analysis with over 30 years of semiconductor industry experience.
Also Read:
Arteris Smart NoC Automation: Accelerating AI-Ready SoC Design in the Era of Chiplets
The IO Hub: An Emerging Pattern for System Connectivity in Chiplet-Based Designs
Arteris Simplifies Design Reuse with Magillem Packaging
Share this post via:




Comments
There are no comments yet.
You must register or log in to view/post comments.