Semiconductor manufacturing is among the most complex industrial activities in existence. As device geometries shrink and systems become more interconnected, software has become as critical as process technology itself. Modern fabs depend on extensive automation, real-time analytics, and deep integration between tools, control systems, and external partners. This complexity dramatically expands the cyber-attack surface, making cybersecurity not just an adhoc or adjunct concern, but rather a core operational challenge.
A typical fab environment includes hundreds of thousands of software components sourced from hundreds of suppliers, continuously updated and interdependent. In such an environment, cybersecurity incidents are inevitable. A widely cited malware incident that halted production at a major fab several years ago marked a turning point for the industry, shifting cybersecurity from a theoretical IT concern to an operational imperative with direct revenue and safety implications.
Why Legacy Security Models Are Breaking Down
Historically, fabs relied on isolation, obscurity, and extreme caution around change. Systems were kept static, external connectivity was minimized, and any untested modification was treated as a production risk. While this approach reduced short-term disruption, it created brittle environments poorly suited to modern threat dynamics.
Today, effective cybersecurity requires continuous patching, operating system updates, software lifecycle management, and rapid response to emerging vulnerabilities. These requirements conflict directly with the reality that changes in a fab environment demand extensive validation. The result is long exposure windows at precisely the moment when attackers are becoming faster, more targeted, and more persistent, often aided by AI.
Security by obscurity no longer works. Semiconductor manufacturing is a high-value target, and fragmented VPNs, ad-hoc access paths, and inconsistent controls increase risk by reducing visibility and slowing response.
Standards Define Only the Foundation, Not the Full Solution
SEMI cybersecurity standards such as E187, E188, and E191 provide an essential baseline. They establish expectations for malware-free equipment, procedural cybersecurity practices, and automated software inventory reporting. Importantly, these standards define what must be protected while intentionally avoiding prescriptive architectural mandates.
This is by design. However, risk emerges when standards are treated as a ceiling rather than a floor. Compliance alone does not define a secure system. Architectures must be designed around zero trust principles such as least privilege, segmentation, continuous validation, and “assumed breach”. In practice, systems designed with these principles in mind are often better positioned to meet both current and future requirements.
Collaboration Is the New Security Frontier
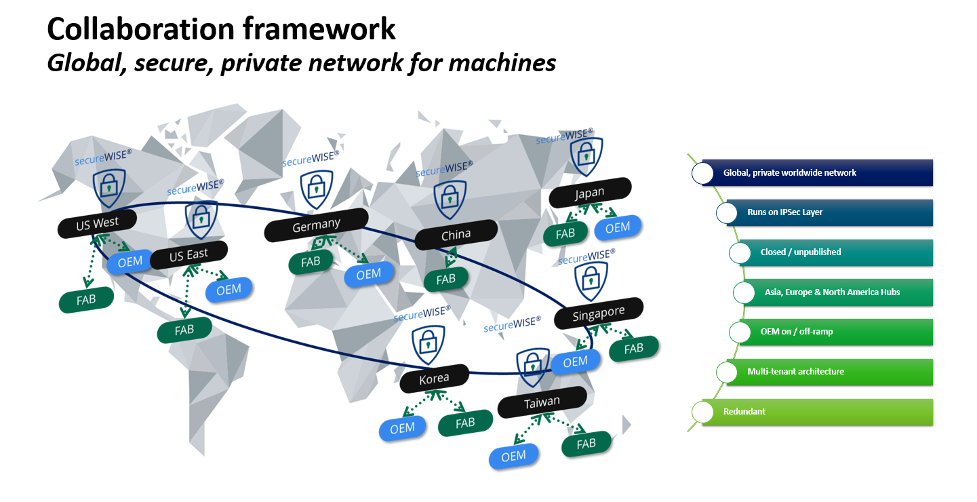
The semiconductor industry now operates as a deeply collaborative global ecosystem. Technology development depends on constant interaction between fabs, solution providers, equipment suppliers, designers, OSATs, and advanced packaging partners. This level of collaboration cannot function in air-gapped environments, yet naive use of public internet connectivity introduces unacceptable risk.
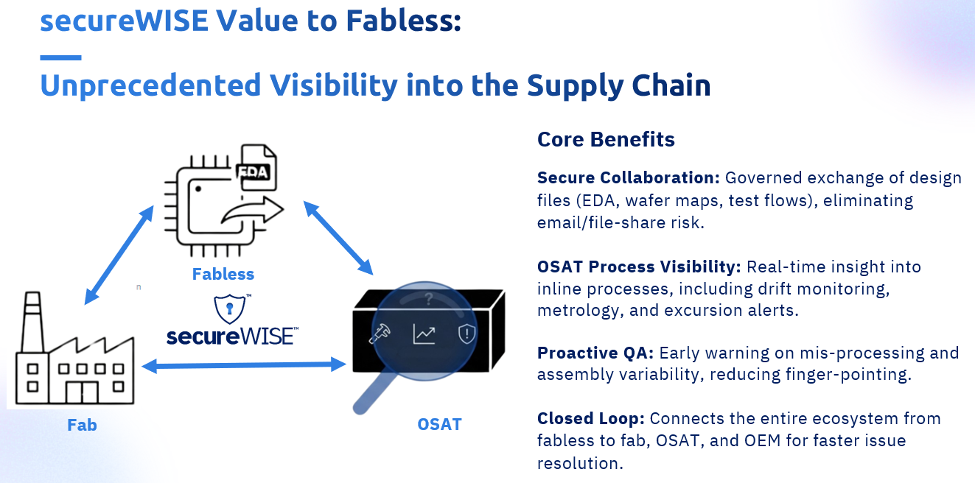
Collaboration has therefore become the new security frontier. The challenge is no longer whether data and access should be shared, but rather how to enable collaboration without exposing proprietary process knowledge, yield signatures, or AI models that define competitive advantage.
Why Secure Collaboration Requires More Than VPNs
Point-to-point VPN models do not scale in this environment. As collaboration grows, VPN sprawl leads to operational complexity, inconsistent governance, and expanding attack surfaces. Each additional tunnel increases firewall exposure and administrative burden while reducing overall visibility.
What is required instead is a framework-based approach in which secure connectivity is centrally managed, segmented, and dynamically enabled. In such models, connectivity is simplified structurally while security is strengthened architecturally.
How secureWISE Operationalizes a Purpose-Built Framework
secureWISE, from PDF Solutions, illustrates how a governed connectivity framework can be purpose-built for semiconductor manufacturing rather than adapted from enterprise information technology (IT) or generic operational technology (OT) solutions.
Over more than 20 years of continuous deployment, secureWISE has been embedded into fab operations worldwide, supporting thousands of tools and global supplier ecosystems under real production constraints. That longevity reflects not only adoption, but sustained trust under conditions of high concurrency, strict uptime requirements, and evolving threat models.
secureWISE’s architectural strength lies in simplification as a security strategy. It replaces a dense mesh of OEM-specific VPNs with a single governed entry point per fab. By collapsing connectivity sprawl into a controlled framework, firewall routing complexity is reduced; custom network engineering is simplified for onboarding and offboarding of endpoints, and the overall attack surface shrinks. What appears operationally simpler is, in fact, more secure.
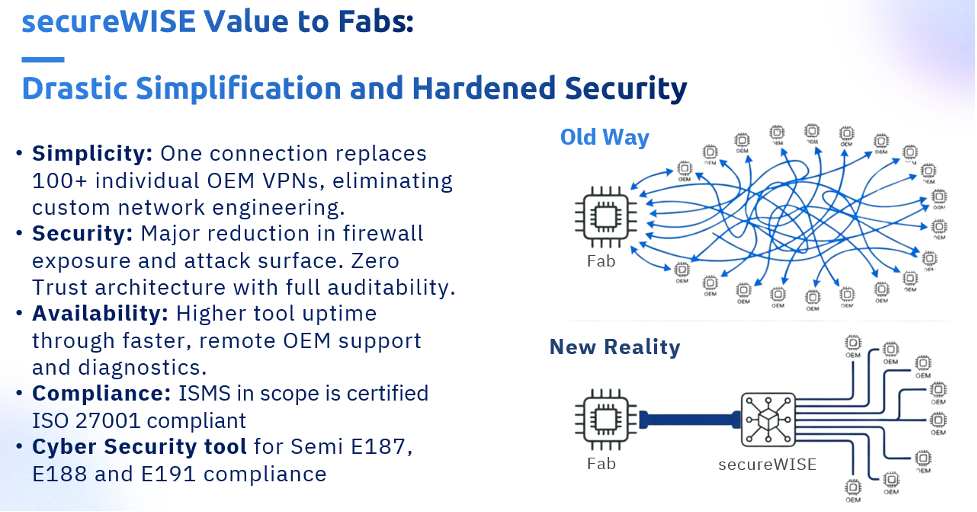
Built around Zero Trust principles, secureWISE enforces identity-centric access with exceptional granularity. Access is not extended merely by network location but is constrained by role, action, context, and purpose.
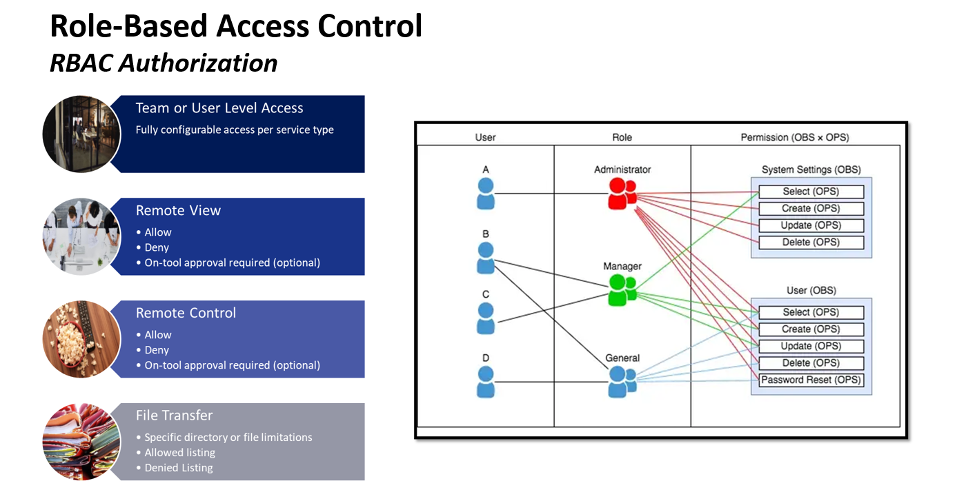
Every session, file transfer, and operation is encrypted, monitored, and logged, providing continuous visibility and long-retention audit trails aligned with ISO 27001 controls and practical compliance with SEMI E187, E188, and E191.
Zero Trust as a Principle, Not a Product
Zero Trust is best understood as a mindset: always verify, assume a possible compromise, and monitor continuously. Effective implementations focus on containment, visibility, and control rather than the unrealistic goal of perfect prevention.
Private networks play a critical role in this approach. By avoiding public internet traffic exposure and explicitly defining allowed routes and participants, attack surfaces are reduced and anomalous behavior becomes easier to detect. Continuous monitoring of access patterns, behavior, and data flows is essential, not only to counter external threats but to manage insider and supply-chain risks.
Proven Architectures Build Long-Term Trust
Ultimately, security is measured by outcomes. Architectures that have enabled global collaboration for decades without material data breaches demonstrate the value of thoughtful design, layered controls, and disciplined execution. These approaches have proven that security can scale alongside the growing complexity of the semiconductor industry.
Standardized, governed connectivity at scale is not merely a security enhancement; it is a marker of operational maturity. It enables collaboration, visibility, and continuous assurance without disrupting production or slowing innovation.
Summary
The semiconductor industry no longer faces a binary choice between openness and security. Collaboration is already happening; the real decision is whether it continues through fragmented, opaque mechanisms or evolves into governed, auditable frameworks designed for scale.
Standards define the foundation. Compliance confirms intent. Long-term security emerges when architectures are purpose-built around real fab workflows, legacy constraints, and global ecosystems. Time-proven frameworks demonstrate that simplification and hardening are not opposing goals but rather mutually reinforcing goals. This is how secure semiconductor collaboration is operationalized safely, globally, and at scale, while staying ahead of an increasingly complex threat landscape.
Also Read:
Why PDF Solutions Is Positioning Itself at the Center of the Semiconductor Ecosystem
Manufacturing Is Strategy: Leadership Lessons from the Semiconductor Front Lines
PDF Solutions’ AI-Driven Collaboration & Smarter Decisions
Share this post via:




Comments
There are no comments yet.
You must register or log in to view/post comments.