You are currently viewing SemiWiki as a guest which gives you limited access to the site. To view blog comments and experience other SemiWiki features you must be a registered member. Registration is fast, simple, and absolutely free so please,
join our community today!
by Jagadish Nayak
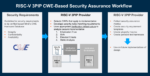
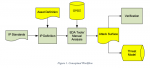
RISC-V adoption continues to accelerate across commercial and government microelectronics programs. Whether open-source or commercially licensed, most RISC-V processor cores are integrated as third-party IP (3PIP), potentially introducing supply chain security challenges that demand structured,… Read More
As RISC-V adoption accelerates across the semiconductor industry, so do the concerns about hardware security vulnerabilities that arise from its open and highly customizable nature. From hardware to firmware and operating systems, every layer of a system-on-chip (SoC) design must be scrutinized for security risks. Unlike… Read More
Security is a slippery topic. We all agree that “something should be done”, but most of us are waiting for someone else to lead the way. There’s no shortage of proprietary solutions, though given the distributed nature of the problem it’s difficult to see how those separately or collectively can rise to the occasion. What we really… Read More
You can update ..Generally, I’m a fan of letting market forces figure out best solutions to whatever evolving needs we may have, but I’m enough of a realist to accept that’s not a workable answer to every need. Some problems need a top-down fix. However, we can’t expect policymakers or industry consortia to create compliance demands… Read More
As I have mentioned before SemiWiki gets to meet some very smart people and here is another one. Scot Morrison has an MS degree in Aerospace Engineering from MIT specializing in control systems. Today he is the general manager of the Embedded Platform Solutions Division at Mentor, a Siemens business. Scot oversees the Linux®, Nucleus®,… Read More
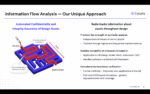
Security has been a domain blessed with an abundance of methods to improve in various ways, not so much in methods to measure the effectiveness of those improvements. With the best will in the world, absent an agreed security measurement, all those improvement techniques still add up to “trust me, our baby monitor camera is really… Read More
I mentioned some time ago (a DVCon or two ago) that Accellera had started working on a standard to quantify IP security. At the time I talked about some of the challenges in the task but nevertheless applauded the effort. You’ve got to start somewhere and some way to quantify this is better than none, as long as it doesn’t deliver misleading… Read More