You are currently viewing SemiWiki as a guest which gives you limited access to the site. To view blog comments and experience other SemiWiki features you must be a registered member. Registration is fast, simple, and absolutely free so please,
join our community today!
by Jagadish Nayak
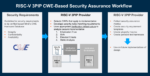
RISC-V adoption continues to accelerate across commercial and government microelectronics programs. Whether open-source or commercially licensed, most RISC-V processor cores are integrated as third-party IP (3PIP), potentially introducing supply chain security challenges that demand structured,… Read More
You can update ..Generally, I’m a fan of letting market forces figure out best solutions to whatever evolving needs we may have, but I’m enough of a realist to accept that’s not a workable answer to every need. Some problems need a top-down fix. However, we can’t expect policymakers or industry consortia to create compliance demands… Read More
Security has been a domain blessed with an abundance of methods to improve in various ways, not so much in methods to measure the effectiveness of those improvements. With the best will in the world, absent an agreed security measurement, all those improvement techniques still add up to “trust me, our baby monitor camera is really… Read More